Search Results for author: Arghya Pal
Found 8 papers, 4 papers with code
Distilling the Undistillable: Learning from a Nasty Teacher
1 code implementation • 21 Oct 2022 • Surgan Jandial, Yash Khasbage, Arghya Pal, Vineeth N Balasubramanian, Balaji Krishnamurthy
The inadvertent stealing of private/sensitive information using Knowledge Distillation (KD) has been getting significant attention recently and has guided subsequent defense efforts considering its critical nature.
A Deep Learning Approach Using Masked Image Modeling for Reconstruction of Undersampled K-spaces
1 code implementation • 24 Aug 2022 • Kyler Larsen, Arghya Pal, Yogesh Rathi
The model was evaluated through L1 loss, gradient normalization, and structural similarity values.
A review and experimental evaluation of deep learning methods for MRI reconstruction
no code implementations • 17 Sep 2021 • Arghya Pal, Yogesh Rathi
Given the rapidly growing nature of the field, it is imperative to consolidate and summarize the large number of deep learning methods that have been reported in the literature, to obtain a better understanding of the field in general.
Synthesize-It-Classifier: Learning a Generative Classifier Through Recurrent Self-Analysis
no code implementations • CVPR 2021 • Arghya Pal, Raphael C.-W. Phan, KokSheik Wong
During training, the classifier iteratively uses these synthesized images as fake samples and re-estimates the class boundary in a recurrent fashion to improve both the classification accuracy and quality of synthetic images.
Synthesize-It-Classifier: Learning a Generative Classifier through RecurrentSelf-analysis
no code implementations • 26 Mar 2021 • Arghya Pal, Rapha Phan, KokSheik Wong
During training, the classifier iteratively uses these synthesized images as fake samples and re-estimates the class boundary in a recurrent fashion to improve both the classification accuracy and quality of synthetic images.
Generative Adversarial Data Programming
no code implementations • 30 Apr 2020 • Arghya Pal, Vineeth N. Balasubramanian
The paucity of large curated hand-labeled training data forms a major bottleneck in the deployment of machine learning models in computer vision and other fields.
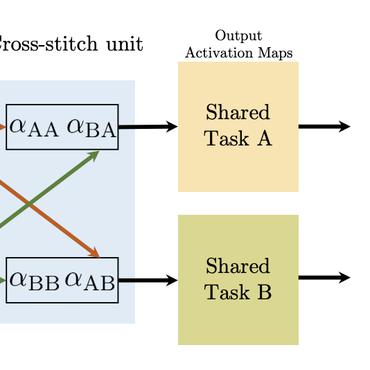
Zero-Shot Task Transfer
1 code implementation • CVPR 2019 • Arghya Pal, Vineeth N. Balasubramanian
Our proposed methodology out-performs state-of-the-art models (which use ground truth)on each of our zero-shot tasks, showing promise on zero-shot task transfer.
Adversarial Data Programming: Using GANs to Relax the Bottleneck of Curated Labeled Data
1 code implementation • CVPR 2018 • Arghya Pal, Vineeth N. Balasubramanian
In this work, we present Adversarial Data Programming (ADP), which presents an adversarial methodology to generate data as well as a curated aggregated label has given a set of weak labeling functions.