Search Results for author: Qiben Yan
Found 11 papers, 0 papers with code
Privacy-Preserving Diffusion Model Using Homomorphic Encryption
no code implementations • 9 Mar 2024 • Yaojian Chen, Qiben Yan
In this paper, we introduce a privacy-preserving stable diffusion framework leveraging homomorphic encryption, called HE-Diffusion, which primarily focuses on protecting the denoising phase of the diffusion process.
Beyond Boundaries: A Comprehensive Survey of Transferable Attacks on AI Systems
no code implementations • 20 Nov 2023 • Guangjing Wang, Ce Zhou, Yuanda Wang, Bocheng Chen, Hanqing Guo, Qiben Yan
This survey offers a holistic understanding of the prevailing transferable attacks and their impacts across different domains.
MASTERKEY: Practical Backdoor Attack Against Speaker Verification Systems
no code implementations • 13 Sep 2023 • Hanqing Guo, Xun Chen, Junfeng Guo, Li Xiao, Qiben Yan
In this work, we propose a backdoor attack MASTERKEY, to compromise the SV models.
PhantomSound: Black-Box, Query-Efficient Audio Adversarial Attack via Split-Second Phoneme Injection
no code implementations • 13 Sep 2023 • Hanqing Guo, Guangjing Wang, Yuanda Wang, Bocheng Chen, Qiben Yan, Li Xiao
We significantly enhance the query efficiency and reduce the cost of a successful untargeted and targeted adversarial attack by 93. 1% and 65. 5% compared with the state-of-the-art black-box attacks, using merely ~300 queries (~5 minutes) and ~1, 500 queries (~25 minutes), respectively.
DynamicFL: Balancing Communication Dynamics and Client Manipulation for Federated Learning
no code implementations • 16 Jul 2023 • Bocheng Chen, Nikolay Ivanov, Guangjing Wang, Qiben Yan
Additionally, our long-term greedy strategy in client selection tackles the problem of system performance degradation caused by short-term scheduling in a dynamic network.
Understanding Multi-Turn Toxic Behaviors in Open-Domain Chatbots
no code implementations • 14 Jul 2023 • Bocheng Chen, Guangjing Wang, Hanqing Guo, Yuanda Wang, Qiben Yan
The chatbot is fine-tuned with a collection of crafted conversation sequences.
A Comprehensive Survey on Pretrained Foundation Models: A History from BERT to ChatGPT
no code implementations • 18 Feb 2023 • Ce Zhou, Qian Li, Chen Li, Jun Yu, Yixin Liu, Guangjing Wang, Kai Zhang, Cheng Ji, Qiben Yan, Lifang He, Hao Peng, JianXin Li, Jia Wu, Ziwei Liu, Pengtao Xie, Caiming Xiong, Jian Pei, Philip S. Yu, Lichao Sun
This study provides a comprehensive review of recent research advancements, challenges, and opportunities for PFMs in text, image, graph, as well as other data modalities.
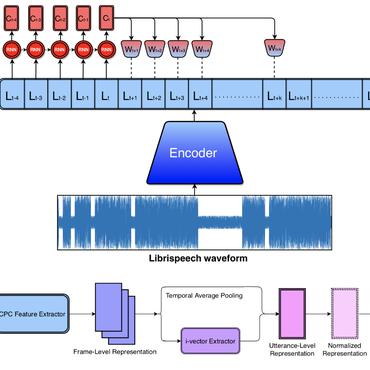
SuperVoice: Text-Independent Speaker Verification Using Ultrasound Energy in Human Speech
no code implementations • 28 May 2022 • Hanqing Guo, Qiben Yan, Nikolay Ivanov, Ying Zhu, Li Xiao, Eric J. Hunter
Our evaluation shows that SUPERVOICE achieves 0. 58% equal error rate in the speaker verification task, it only takes 120 ms for testing an incoming utterance, outperforming all existing speaker verification systems.
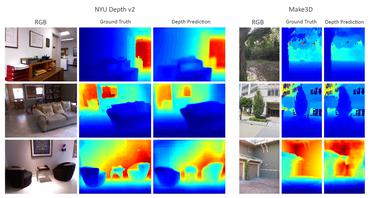
DoubleStar: Long-Range Attack Towards Depth Estimation based Obstacle Avoidance in Autonomous Systems
no code implementations • 7 Oct 2021 • Ce Zhou, Qiben Yan, Yan Shi, Lichao Sun
By exploiting the weaknesses of the stereo matching in depth estimation algorithms and the lens flare effect in optical imaging, we propose DoubleStar, a long-range attack that injects fake obstacle depth by projecting pure light from two complementary light sources.
Constraint-Based Inference of Heuristics for Foreign Exchange Trade Model Optimization
no code implementations • 11 May 2021 • Nikolay Ivanov, Qiben Yan
The Foreign Exchange (Forex) is a large decentralized market, on which trading analysis and algorithmic trading are popular.
Generating Robust Audio Adversarial Examples using Iterative Proportional Clipping
no code implementations • 25 Sep 2019 • Hongting Zhang, Qiben Yan, Pan Zhou
We then impose a constraint on the perturbation at the positions with lower sound intensity across the time domain to eliminate the perceptible noise during the silent periods or pauses.
 Automatic Speech Recognition
Automatic Speech Recognition
 Automatic Speech Recognition (ASR)
+1
Automatic Speech Recognition (ASR)
+1