Search Results for author: Triet H. M. Le
Found 8 papers, 6 papers with code
Are Latent Vulnerabilities Hidden Gems for Software Vulnerability Prediction? An Empirical Study
1 code implementation • 20 Jan 2024 • Triet H. M. Le, Xiaoning Du, M. Ali Babar
To bridge these gaps, we conduct a large-scale study on the latent vulnerable functions in two commonly used SV datasets and their utilization for function-level and line-level SV predictions.
Towards an Improved Understanding of Software Vulnerability Assessment Using Data-Driven Approaches
no code implementations • 24 Jul 2022 • Triet H. M. Le
The thesis advances the field of software security by providing knowledge and automation support for software vulnerability assessment using data-driven approaches.
On the Use of Fine-grained Vulnerable Code Statements for Software Vulnerability Assessment Models
1 code implementation • 16 Mar 2022 • Triet H. M. Le, M. Ali Babar
We show that vulnerable statements are 5. 8 times smaller in size, yet exhibit 7. 5-114. 5% stronger assessment performance (Matthews Correlation Coefficient (MCC)) than non-vulnerable statements.
Automated Security Assessment for the Internet of Things
no code implementations • 9 Sep 2021 • Xuanyu Duan, Mengmeng Ge, Triet H. M. Le, Faheem Ullah, Shang Gao, Xuequan Lu, M. Ali Babar
This security model automatically assesses the security of the IoT network by capturing potential attack paths.
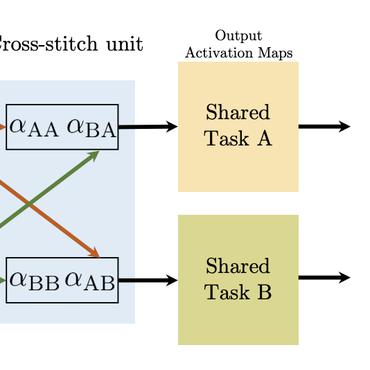
DeepCVA: Automated Commit-level Vulnerability Assessment with Deep Multi-task Learning
1 code implementation • 18 Aug 2021 • Triet H. M. Le, David Hin, Roland Croft, M. Ali Babar
It is increasingly suggested to identify Software Vulnerabilities (SVs) in code commits to give early warnings about potential security risks.
A Survey on Data-driven Software Vulnerability Assessment and Prioritization
1 code implementation • 18 Jul 2021 • Triet H. M. Le, Huaming Chen, M. Ali Babar
Software Vulnerabilities (SVs) are increasing in complexity and scale, posing great security risks to many software systems.
PUMiner: Mining Security Posts from Developer Question and Answer Websites with PU Learning
1 code implementation • 8 Mar 2020 • Triet H. M. Le, David Hin, Roland Croft, M. Ali Babar
Using PUMiner, we provide the largest and up-to-date security content on Q&A websites for practitioners and researchers.
Deep Learning for Source Code Modeling and Generation: Models, Applications and Challenges
1 code implementation • 13 Feb 2020 • Triet H. M. Le, Hao Chen, M. Ali Babar
Deep Learning (DL) techniques for Natural Language Processing have been evolving remarkably fast.