Search Results for author: Yifeng Xiong
Found 17 papers, 4 papers with code
Performance Bounds for Passive Sensing in Asynchronous ISAC Systems -- Appendices
no code implementations • 9 Mar 2024 • Jingbo Zhao, Zhaoming Lu, J. Andrew Zhang, Weicai Li, Yifeng Xiong, Zijun Han, Xiangming Wen, Tao Gu
This document contains the appendices for our paper titled ``Performance Bounds for Passive Sensing in Asynchronous ISAC Systems."
Reshaping the ISAC Tradeoff Under OFDM Signaling: A Probabilistic Constellation Shaping Approach
no code implementations • 26 Dec 2023 • Zhen Du, Fan Liu, Yifeng Xiong, Tony Xiao Han, Yonina C. Eldar, Shi Jin
To cope with this issue, we characterize the random AF of OFDM communication signals, and demonstrate that the AF variance is determined by the fourth-moment of the constellation amplitudes.
Communication-Assisted Sensing in 6G Networks
no code implementations • 13 Nov 2023 • Fuwang Dong, Fan Liu, Shihang Lu, Yifeng Xiong, Qixun Zhang, Zhiyong Feng
Exploring the mutual benefit and reciprocity of sensing and communication (S\&C) functions is fundamental to realizing deeper integration for integrated sensing and communication (ISAC) systems.
Probabilistic Constellation Shaping for OFDM-Based ISAC Signaling
no code implementations • 27 Oct 2023 • Zhen Du, Fan Liu, Yifeng Xiong, Tony Xiao Han, Weijie Yuan, Yuanhao Cui, Changhua Yao, Yonina C. Eldar
Integrated Sensing and Communications (ISAC) has garnered significant attention as a promising technology for the upcoming sixth-generation wireless communication systems (6G).
Light Field Diffusion for Single-View Novel View Synthesis
no code implementations • 20 Sep 2023 • Yifeng Xiong, Haoyu Ma, Shanlin Sun, Kun Han, Hao Tang, Xiaohui Xie
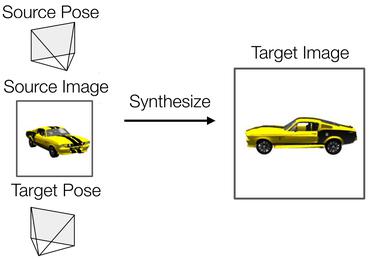
Starting from the camera pose matrices, LFD transforms them into light field encoding, with the same shape as the reference image, to describe the direction of each ray.
Sensing With Random Signals
no code implementations • 5 Sep 2023 • Shihang Lu, Fan Liu, Fuwang Dong, Yifeng Xiong, Jie Xu, Ya-Feng Liu
Radar systems typically employ well-designed deterministic signals for target sensing.
Waveform Design for Communication-Assisted Sensing in 6G Perceptive Networks
no code implementations • 19 May 2023 • Fuwang Dong, Fan Liu, Shihang Lu, Weijie Yuan, Yuanhao Cui, Yifeng Xiong, Feifei Gao
In particular, a pair of transmission schemes, namely, separated S&C and dual-functional waveform designs, are proposed to optimize the sensing QoS under the constraints of the rate-distortion and power budget.
MedGen3D: A Deep Generative Framework for Paired 3D Image and Mask Generation
no code implementations • 8 Apr 2023 • Kun Han, Yifeng Xiong, Chenyu You, Pooya Khosravi, Shanlin Sun, Xiangyi Yan, James Duncan, Xiaohui Xie
Then, we use an image sequence generator and semantic diffusion refiner conditioned on the generated mask sequences to produce realistic 3D medical images that align with the generated masks.
Rethinking Estimation Rate for Wireless Sensing: A Rate-Distortion Perspective
no code implementations • 21 Mar 2023 • Fuwang Dong, Fan Liu, Shihang Lu, Yifeng Xiong
Wireless sensing has been recognized as a key enabling technology for numerous emerging applications.
Semantic Adversarial Attacks on Face Recognition through Significant Attributes
no code implementations • 28 Jan 2023 • Yasmeen M. Khedr, Yifeng Xiong, Kun He
The probability score method is based on training a Face Verification model for an attribute prediction task to obtain a class probability score for each attribute.
Joint Receiver Design for Integrated Sensing and Communications
1 code implementation • 10 Nov 2022 • Yuxiang Dong, Fan Liu, Yifeng Xiong
In this letter, we investigate the joint receiver design for integrated sensing and communication (ISAC) systems, where the communication signal and the target echo signal are simultaneously received and processed to achieve a balanced performance between both functionalities.
On the Performance Gain of Integrated Sensing and Communications: A Subspace Correlation Perspective
no code implementations • 1 Nov 2022 • Shihang Lu, Xiao Meng, Zhen Du, Yifeng Xiong, Fan Liu
In this paper, we shed light on the performance gain of integrated sensing and communications (ISAC) from the perspective of channel correlations between radar sensing and communication (S&C), namely ISAC subspace correlation.
Sampling-based Fast Gradient Rescaling Method for Highly Transferable Adversarial Attacks
1 code implementation • 6 Apr 2022 • Xu Han, Anmin Liu, Yifeng Xiong, Yanbo Fan, Kun He
Deviation between the original gradient and the generated noises may lead to inaccurate gradient update estimation and suboptimal solutions for adversarial transferability, which is crucial for black-box attacks.
Stochastic Variance Reduced Ensemble Adversarial Attack for Boosting the Adversarial Transferability
1 code implementation • CVPR 2022 • Yifeng Xiong, Jiadong Lin, Min Zhang, John E. Hopcroft, Kun He
The black-box adversarial attack has attracted impressive attention for its practical use in the field of deep learning security.
Stochastic Variance Reduced Ensemble Adversarial Attack
no code implementations • 29 Sep 2021 • Jiadong Lin, Yifeng Xiong, Min Zhang, John E. Hopcroft, Kun He
Black-box adversarial attack has attracted much attention for its practical use in deep learning applications, and it is very challenging as there is no access to the architecture and weights of the target model.
Detecting Textual Adversarial Examples through Randomized Substitution and Vote
1 code implementation • 13 Sep 2021 • Xiaosen Wang, Yifeng Xiong, Kun He
Based on this observation, we propose a novel textual adversarial example detection method, termed Randomized Substitution and Vote (RS&V), which votes the prediction label by accumulating the logits of k samples generated by randomly substituting the words in the input text with synonyms.
Sampling Overhead Analysis of Quantum Error Mitigation: Uncoded vs. Coded Systems
no code implementations • 15 Dec 2020 • Yifeng Xiong, Daryus Chandra, Soon Xin Ng, Lajos Hanzo
Quantum error mitigation (QEM) is a promising technique of protecting hybrid quantum-classical computation from decoherence, but it suffers from sampling overhead which erodes the computational speed.
Quantum Physics Information Theory Information Theory