Search Results for author: Yves Le Traon
Found 32 papers, 15 papers with code
Constrained Adaptive Attacks: Realistic Evaluation of Adversarial Examples and Robust Training of Deep Neural Networks for Tabular Data
no code implementations • 8 Nov 2023 • Thibault Simonetto, Salah Ghamizi, Antoine Desjardins, Maxime Cordy, Yves Le Traon
State-of-the-art deep learning models for tabular data have recently achieved acceptable performance to be deployed in industrial settings.
Evaluating the Robustness of Test Selection Methods for Deep Neural Networks
no code implementations • 29 Jul 2023 • Qiang Hu, Yuejun Guo, Xiaofei Xie, Maxime Cordy, Wei Ma, Mike Papadakis, Yves Le Traon
Testing deep learning-based systems is crucial but challenging due to the required time and labor for labeling collected raw data.
CodeLens: An Interactive Tool for Visualizing Code Representations
no code implementations • 27 Jul 2023 • Yuejun Guo, Seifeddine Bettaieb, Qiang Hu, Yves Le Traon, Qiang Tang
Representing source code in a generic input format is crucial to automate software engineering tasks, e. g., applying machine learning algorithms to extract information.
A Black-Box Attack on Code Models via Representation Nearest Neighbor Search
no code implementations • 10 May 2023 • Jie Zhang, Wei Ma, Qiang Hu, Shangqing Liu, Xiaofei Xie, Yves Le Traon, Yang Liu
Furthermore, the perturbation of adversarial examples introduced by RNNS is smaller compared to the baselines in terms of the number of replaced variables and the change in variable length.
Distribution-aware Fairness Test Generation
no code implementations • 8 May 2023 • Sai Sathiesh Rajan, Ezekiel Soremekun, Yves Le Traon, Sudipta Chattopadhyay
This work addresses how to validate group fairness in image recognition software.
Going Further: Flatness at the Rescue of Early Stopping for Adversarial Example Transferability
1 code implementation • 5 Apr 2023 • Martin Gubri, Maxime Cordy, Yves Le Traon
A common hypothesis to explain this is that deep neural networks (DNNs) first learn robust features, which are more generic, thus a better surrogate.
Boosting Source Code Learning with Data Augmentation: An Empirical Study
no code implementations • 13 Mar 2023 • Zeming Dong, Qiang Hu, Yuejun Guo, Zhenya Zhang, Maxime Cordy, Mike Papadakis, Yves Le Traon, Jianjun Zhao
The next era of program understanding is being propelled by the use of machine learning to solve software problems.
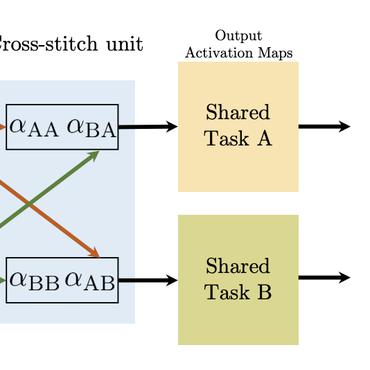
GAT: Guided Adversarial Training with Pareto-optimal Auxiliary Tasks
1 code implementation • 6 Feb 2023 • Salah Ghamizi, Jingfeng Zhang, Maxime Cordy, Mike Papadakis, Masashi Sugiyama, Yves Le Traon
While leveraging additional training data is well established to improve adversarial robustness, it incurs the unavoidable cost of data collection and the heavy computation to train models.
On Evaluating Adversarial Robustness of Chest X-ray Classification: Pitfalls and Best Practices
no code implementations • 15 Dec 2022 • Salah Ghamizi, Maxime Cordy, Michail Papadakis, Yves Le Traon
Vulnerability to adversarial attacks is a well-known weakness of Deep Neural Networks.
MIXCODE: Enhancing Code Classification by Mixup-Based Data Augmentation
1 code implementation • 6 Oct 2022 • Zeming Dong, Qiang Hu, Yuejun Guo, Maxime Cordy, Mike Papadakis, Zhenya Zhang, Yves Le Traon, Jianjun Zhao
Data augmentation has been a popular approach to supplement training data in domains such as computer vision and NLP.
On the Effectiveness of Hybrid Pooling in Mixup-Based Graph Learning for Language Processing
no code implementations • 6 Oct 2022 • Zeming Dong, Qiang Hu, Zhenya Zhang, Yuejun Guo, Maxime Cordy, Mike Papadakis, Yves Le Traon, Jianjun Zhao
Graph neural network (GNN)-based graph learning has been popular in natural language and programming language processing, particularly in text and source code classification.
LGV: Boosting Adversarial Example Transferability from Large Geometric Vicinity
1 code implementation • 26 Jul 2022 • Martin Gubri, Maxime Cordy, Mike Papadakis, Yves Le Traon, Koushik Sen
We propose transferability from Large Geometric Vicinity (LGV), a new technique to increase the transferability of black-box adversarial attacks.
Aries: Efficient Testing of Deep Neural Networks via Labeling-Free Accuracy Estimation
1 code implementation • 22 Jul 2022 • Qiang Hu, Yuejun Guo, Xiaofei Xie, Maxime Cordy, Lei Ma, Mike Papadakis, Yves Le Traon
Recent studies show that test selection for DNN is a promising direction that tackles this issue by selecting minimal representative data to label and using these data to assess the model.
CodeS: Towards Code Model Generalization Under Distribution Shift
2 code implementations • 11 Jun 2022 • Qiang Hu, Yuejun Guo, Xiaofei Xie, Maxime Cordy, Lei Ma, Mike Papadakis, Yves Le Traon
Distribution shift has been a longstanding challenge for the reliable deployment of deep learning (DL) models due to unexpected accuracy degradation.
LaF: Labeling-Free Model Selection for Automated Deep Neural Network Reusing
1 code implementation • 8 Apr 2022 • Qiang Hu, Yuejun Guo, Maxime Cordy, Xiaofei Xie, Mike Papadakis, Yves Le Traon
Applying deep learning to science is a new trend in recent years which leads DL engineering to become an important problem.
Characterizing and Understanding the Behavior of Quantized Models for Reliable Deployment
1 code implementation • 8 Apr 2022 • Qiang Hu, Yuejun Guo, Maxime Cordy, Xiaofei Xie, Wei Ma, Mike Papadakis, Yves Le Traon
The results reveal that 1) data with distribution shifts happen more disagreements than without.
On The Empirical Effectiveness of Unrealistic Adversarial Hardening Against Realistic Adversarial Attacks
1 code implementation • 7 Feb 2022 • Salijona Dyrmishi, Salah Ghamizi, Thibault Simonetto, Yves Le Traon, Maxime Cordy
While the literature on security attacks and defense of Machine Learning (ML) systems mostly focuses on unrealistic adversarial examples, recent research has raised concern about the under-explored field of realistic adversarial attacks and their implications on the robustness of real-world systems.
Robust Active Learning: Sample-Efficient Training of Robust Deep Learning Models
no code implementations • 5 Dec 2021 • Yuejun Guo, Qiang Hu, Maxime Cordy, Mike Papadakis, Yves Le Traon
Our acquisition function -- named density-based robust sampling with entropy (DRE) -- outperforms the other acquisition functions (including random) in terms of robustness by up to 24. 40\% (3. 84\% than random particularly), while remaining competitive on accuracy.
A Unified Framework for Adversarial Attack and Defense in Constrained Feature Space
no code implementations • 2 Dec 2021 • Thibault Simonetto, Salijona Dyrmishi, Salah Ghamizi, Maxime Cordy, Yves Le Traon
We propose a unified framework to generate feasible adversarial examples that satisfy given domain constraints.
Adversarial Robustness in Multi-Task Learning: Promises and Illusions
1 code implementation • 26 Oct 2021 • Salah Ghamizi, Maxime Cordy, Mike Papadakis, Yves Le Traon
Vulnerability to adversarial attacks is a well-known weakness of Deep Neural networks.
MUTEN: Boosting Gradient-Based Adversarial Attacks via Mutant-Based Ensembles
no code implementations • 27 Sep 2021 • Yuejun Guo, Qiang Hu, Maxime Cordy, Michail Papadakis, Yves Le Traon
In this paper, we propose MUTEN, a low-cost method to improve the success rate of well-known attacks against gradient-masking models.
Learning from What We Know: How to Perform Vulnerability Prediction using Noisy Historical Data
1 code implementation • 21 Dec 2020 • Aayush Garg, Renzo Degiovanni, Matthieu Jimenez, Maxime Cordy, Mike Papadakis, Yves Le Traon
To tackle these issues, we propose TROVON, a technique that learns from known vulnerable components rather than from vulnerable and non-vulnerable components, as typically performed.
 Machine Translation
Cryptography and Security
Software Engineering
Machine Translation
Cryptography and Security
Software Engineering
Influence-Driven Data Poisoning in Graph-Based Semi-Supervised Classifiers
no code implementations • 14 Dec 2020 • Adriano Franci, Maxime Cordy, Martin Gubri, Mike Papadakis, Yves Le Traon
Graph-based Semi-Supervised Learning (GSSL) is a practical solution to learn from a limited amount of labelled data together with a vast amount of unlabelled data.
IBIR: Bug Report driven Fault Injection
no code implementations • 11 Dec 2020 • Ahmed Khanfir, Anil Koyuncu, Mike Papadakis, Maxime Cordy, Tegawendé F. Bissyandé, Jacques Klein, Yves Le Traon
It remains indeed challenging to inject few but realistic faults that target a particular functionality in a program.
 Fault Detection
Fault Detection
 Program Repair
+2
Software Engineering
Program Repair
+2
Software Engineering
Efficient and Transferable Adversarial Examples from Bayesian Neural Networks
1 code implementation • 10 Nov 2020 • Martin Gubri, Maxime Cordy, Mike Papadakis, Yves Le Traon, Koushik Sen
An established way to improve the transferability of black-box evasion attacks is to craft the adversarial examples on an ensemble-based surrogate to increase diversity.
Adversarial Embedding: A robust and elusive Steganography and Watermarking technique
no code implementations • 14 Nov 2019 • Salah Ghamizi, Maxime Cordy, Mike Papadakis, Yves Le Traon
The key idea of our method is to use deep neural networks for image classification and adversarial attacks to embed secret information within images.
iFixR: Bug Report driven Program Repair
2 code implementations • 12 Jul 2019 • Anil Koyuncu, Kui Liu, Tegawendé F. Bissyandé, Dongsun Kim, Martin Monperrus, Jacques Klein, Yves Le Traon
Towards increasing the adoption of patch generation tools by practitioners, we investigate a new repair pipeline, iFixR, driven by bug reports: (1) bug reports are fed to an IR-based fault localizer; (2) patches are generated from fix patterns and validated via regression testing; (3) a prioritized list of generated patches is proposed to developers.
Software Engineering
Test Selection for Deep Learning Systems
no code implementations • 30 Apr 2019 • Wei Ma, Mike Papadakis, Anestis Tsakmalis, Maxime Cordy, Yves Le Traon
This raises the question of how we can automatically select candidate test data to test deep learning models.
Automated Search for Configurations of Deep Neural Network Architectures
1 code implementation • 9 Apr 2019 • Salah Ghamizi, Maxime Cordy, Mike Papadakis, Yves Le Traon
First, we model the variability of DNN architectures with a Feature Model (FM) that generalizes over existing architectures.
Watch out for This Commit! A Study of Influential Software Changes
no code implementations • 10 Jun 2016 • Daoyuan Li, Li Li, Dongsun Kim, Tegawendé F. Bissyandé, David Lo, Yves Le Traon
One single code change can significantly influence a wide range of software systems and their users.
Software Engineering
Assessing and Improving the Mutation Testing Practice of PIT
1 code implementation • 11 Jan 2016 • Thomas Laurent, Anthony Ventresque, Mike Papadakis, Christopher Henard, Yves Le Traon
We therefore examine how effective are the mutants of a popular mutation testing tool, named PIT, compared to comprehensive ones, as drawn from the literature and personal experience.
Software Engineering
Artificial Mutation inspired Hyper-heuristic for Runtime Usage of Multi-objective Algorithms
no code implementations • 18 Feb 2014 • Donia El Kateb, François Fouquet, Johann Bourcier, Yves Le Traon
In the last years, multi-objective evolutionary algorithms (MOEA) have been applied to different software engineering problems where many conflicting objectives have to be optimized simultaneously.