Search Results for author: Zhengyi Wang
Found 13 papers, 8 papers with code
FlexiDreamer: Single Image-to-3D Generation with FlexiCubes
1 code implementation • 1 Apr 2024 • Ruowen Zhao, Zhengyi Wang, Yikai Wang, Zihan Zhou, Jun Zhu
However, due to the challenge of directly deforming the mesh representation to approach the target topology, most methodologies learn an implicit representation (such as NeRF) during the sparse-view reconstruction and acquire the target mesh by a post-processing extraction.
DreamReward: Text-to-3D Generation with Human Preference
no code implementations • 21 Mar 2024 • Junliang Ye, Fangfu Liu, Qixiu Li, Zhengyi Wang, Yikai Wang, Xinzhou Wang, Yueqi Duan, Jun Zhu
Building upon the 3D reward model, we finally perform theoretical analysis and present the Reward3D Feedback Learning (DreamFL), a direct tuning algorithm to optimize the multi-view diffusion models with a redefined scorer.
V3D: Video Diffusion Models are Effective 3D Generators
2 code implementations • 11 Mar 2024 • Zilong Chen, Yikai Wang, Feng Wang, Zhengyi Wang, Huaping Liu
To fully unleash the potential of video diffusion to perceive the 3D world, we further introduce geometrical consistency prior and extend the video diffusion model to a multi-view consistent 3D generator.
CRM: Single Image to 3D Textured Mesh with Convolutional Reconstruction Model
no code implementations • 8 Mar 2024 • Zhengyi Wang, Yikai Wang, Yifei Chen, Chendong Xiang, Shuo Chen, Dajiang Yu, Chongxuan Li, Hang Su, Jun Zhu
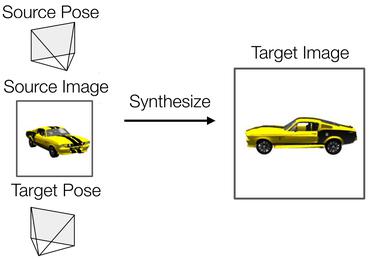
In this work, we present the Convolutional Reconstruction Model (CRM), a high-fidelity feed-forward single image-to-3D generative model.
Observation-Guided Meteorological Field Downscaling at Station Scale: A Benchmark and a New Method
no code implementations • 22 Jan 2024 • Zili Liu, Hao Chen, Lei Bai, Wenyuan Li, Keyan Chen, Zhengyi Wang, Wanli Ouyang, Zhengxia Zou, Zhenwei Shi
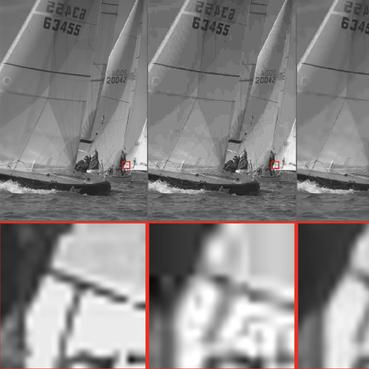
In this paper, we extend meteorological downscaling to arbitrary scattered station scales, establish a brand new benchmark and dataset, and retrieve meteorological states at any given station location from a coarse-resolution meteorological field.
AnimatableDreamer: Text-Guided Non-rigid 3D Model Generation and Reconstruction with Canonical Score Distillation
no code implementations • 6 Dec 2023 • Xinzhou Wang, Yikai Wang, Junliang Ye, Zhengyi Wang, Fuchun Sun, Pengkun Liu, Ling Wang, Kai Sun, Xintong Wang, Bin He
Extensive experiments demonstrate the capability of our method in generating high-flexibility text-guided 3D models from the monocular video, while also showing improved reconstruction performance over existing non-rigid reconstruction methods.
Score Regularized Policy Optimization through Diffusion Behavior
1 code implementation • 11 Oct 2023 • Huayu Chen, Cheng Lu, Zhengyi Wang, Hang Su, Jun Zhu
Recent developments in offline reinforcement learning have uncovered the immense potential of diffusion modeling, which excels at representing heterogeneous behavior policies.
DIFFender: Diffusion-Based Adversarial Defense against Patch Attacks
no code implementations • 15 Jun 2023 • Caixin Kang, Yinpeng Dong, Zhengyi Wang, Shouwei Ruan, Yubo Chen, Hang Su, Xingxing Wei
In this paper, we propose DIFFender, a novel defense method that leverages a text-guided diffusion model to defend against adversarial patches.
ProlificDreamer: High-Fidelity and Diverse Text-to-3D Generation with Variational Score Distillation
2 code implementations • NeurIPS 2023 • Zhengyi Wang, Cheng Lu, Yikai Wang, Fan Bao, Chongxuan Li, Hang Su, Jun Zhu
In comparison, VSD works well with various CFG weights as ancestral sampling from diffusion models and simultaneously improves the diversity and sample quality with a common CFG weight (i. e., $7. 5$).
Robust Classification via a Single Diffusion Model
2 code implementations • 24 May 2023 • Huanran Chen, Yinpeng Dong, Zhengyi Wang, Xiao Yang, Chengqi Duan, Hang Su, Jun Zhu
Since our method does not require training on particular adversarial attacks, we demonstrate that it is more generalizable to defend against multiple unseen threats.
 Ranked #2 on
Adversarial Defense
on CIFAR-10
Ranked #2 on
Adversarial Defense
on CIFAR-10
PREIM3D: 3D Consistent Precise Image Attribute Editing from a Single Image
1 code implementation • CVPR 2023 • Jianhui Li, Jianmin Li, Haoji Zhang, Shilong Liu, Zhengyi Wang, Zihao Xiao, Kaiwen Zheng, Jun Zhu
As for imprecise image editing, we attribute the problem to the gap between the latent space of real images and that of generated images.
GNOT: A General Neural Operator Transformer for Operator Learning
2 code implementations • 28 Feb 2023 • Zhongkai Hao, Zhengyi Wang, Hang Su, Chengyang Ying, Yinpeng Dong, Songming Liu, Ze Cheng, Jian Song, Jun Zhu
However, there are several challenges for learning operators in practical applications like the irregular mesh, multiple input functions, and complexity of the PDEs' solution.
Cluster Attack: Query-based Adversarial Attacks on Graphs with Graph-Dependent Priors
1 code implementation • ICML Workshop AML 2021 • Zhengyi Wang, Zhongkai Hao, Ziqiao Wang, Hang Su, Jun Zhu
In this work, we propose Cluster Attack -- a Graph Injection Attack (GIA) on node classification, which injects fake nodes into the original graph to degenerate the performance of graph neural networks (GNNs) on certain victim nodes while affecting the other nodes as little as possible.