Search Results for author: Mohamed Reda Bouadjenek
Found 13 papers, 1 papers with code
A Distributed Collaborative Filtering Algorithm Using Multiple Data Sources
no code implementations • 16 Jul 2018 • Mohamed Reda Bouadjenek, Esther Pacitti, Maximilien Servajean, Florent Masseglia, Amr El Abbadi
Collaborative Filtering (CF) is one of the most commonly used recommendation methods.
Feature Extraction Functions for Neural Logic Rule Learning
no code implementations • 14 Aug 2020 • Shashank Gupta, Antonio Robles-Kelly, Mohamed Reda Bouadjenek
Combining symbolic human knowledge with neural networks provides a rule-based ante-hoc explanation of the output.
Unintended Bias in Language Model-driven Conversational Recommendation
no code implementations • 17 Jan 2022 • Tianshu Shen, Jiaru Li, Mohamed Reda Bouadjenek, Zheda Mai, Scott Sanner
Conversational Recommendation Systems (CRSs) have recently started to leverage pretrained language models (LM) such as BERT for their ability to semantically interpret a wide range of preference statement variations.
Linked Data Triples Enhance Document Relevance Classification
1 code implementation • Applied Sciences 2021 • Dinesh Nagumothu, Peter W. Eklund, Bahadorreza Ofoghi, Mohamed Reda Bouadjenek
These use an external corpus as a knowledge base that conditions the model to help predict what a document is about.
Adversarial Attacks on Speech Recognition Systems for Mission-Critical Applications: A Survey
no code implementations • 22 Feb 2022 • Ngoc Dung Huynh, Mohamed Reda Bouadjenek, Imran Razzak, Kevin Lee, Chetan Arora, Ali Hassani, Arkady Zaslavsky
Indeed, Adversarial Artificial Intelligence (AI) which refers to a set of techniques that attempt to fool machine learning models with deceptive data, is a growing threat in the AI and machine learning research community, in particular for machine-critical applications.
SHINE: Deep Learning-Based Accessible Parking Management System
no code implementations • 2 Feb 2023 • Dhiraj Neupane, Aashish Bhattarai, Sunil Aryal, Mohamed Reda Bouadjenek, Uk-Min Seok, Jongwon Seok
However, this gradual increment in the number of vehicles has inevitably led to parking-related issues, including the abuse of disabled parking spaces (hereafter referred to as accessible parking spaces) designated for individuals with disabilities.
HUMS2023 Data Challenge Result Submission
no code implementations • 8 Jul 2023 • Dhiraj Neupane, Lakpa Dorje Tamang, Ngoc Dung Huynh, Mohamed Reda Bouadjenek, Sunil Aryal
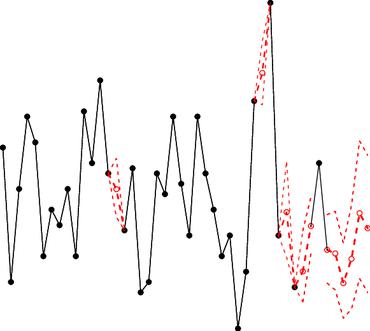
We implemented a simple method for early detection in this research.
Training Machine Learning models at the Edge: A Survey
no code implementations • 5 Mar 2024 • Aymen Rayane Khouas, Mohamed Reda Bouadjenek, Hakim Hacid, Sunil Aryal
This survey delves into Edge Learning (EL), specifically the optimization of ML model training at the edge.
usfAD Based Effective Unknown Attack Detection Focused IDS Framework
no code implementations • 17 Mar 2024 • Md. Ashraf Uddin, Sunil Aryal, Mohamed Reda Bouadjenek, Muna Al-Hawawreh, Md. Alamin Talukder
To address this challenge, we put forth two strategies for semi-supervised learning based IDS where training samples of attacks are not required: 1) training a supervised machine learning model using randomly and uniformly dispersed synthetic attack samples; 2) building a One Class Classification (OCC) model that is trained exclusively on benign network traffic.
Hierarchical Classification for Intrusion Detection System: Effective Design and Empirical Analysis
no code implementations • 17 Mar 2024 • Md. Ashraf Uddin, Sunil Aryal, Mohamed Reda Bouadjenek, Muna Al-Hawawreh, Md. Alamin Talukder
With the increased use of network technologies like Internet of Things (IoT) in many real-world applications, new types of cyberattacks have been emerging.
A Dual-Tier Adaptive One-Class Classification IDS for Emerging Cyberthreats
no code implementations • 17 Mar 2024 • Md. Ashraf Uddin, Sunil Aryal, Mohamed Reda Bouadjenek, Muna Al-Hawawreh, Md. Alamin Talukder
Within this second tier, we also embed a multi-classification mechanism coupled with a clustering algorithm.
The Pursuit of Fairness in Artificial Intelligence Models: A Survey
no code implementations • 26 Mar 2024 • Tahsin Alamgir Kheya, Mohamed Reda Bouadjenek, Sunil Aryal
This survey offers a synopsis of the different ways researchers have promoted fairness in AI systems.
Review for Handling Missing Data with special missing mechanism
no code implementations • 7 Apr 2024 • Youran Zhou, Sunil Aryal, Mohamed Reda Bouadjenek
Understanding what missing data is, how it occurs, and why it is crucial to handle it appropriately is paramount when working with real-world data, especially in tabular data, one of the most commonly used data types in the real world.