Search Results for author: Ke Ma
Found 41 papers, 19 papers with code
Hawk: Learning to Understand Open-World Video Anomalies
no code implementations • 27 May 2024 • Jiaqi Tang, Hao Lu, Ruizheng Wu, Xiaogang Xu, Ke Ma, Cheng Fang, Bin Guo, Jiangbo Lu, Qifeng Chen, Ying-Cong Chen
Video Anomaly Detection (VAD) systems can autonomously monitor and identify disturbances, reducing the need for manual labor and associated costs.
TypeII-CsiNet: CSI Feedback with TypeII Codebook
no code implementations • 21 May 2024 • Yiliang Sang, Ke Ma, Yang Ming, Jin Lian, Zhaocheng Wang
Firstly, a dedicated pre-processing module is designed to sort the selected ports for reserving the correlations of their corresponding coefficients.
Interpretable Machine Learning Enhances Disease Prognosis: Applications on COVID-19 and Onward
no code implementations • 19 May 2024 • Jinzhi Shen, Ke Ma
In response to the COVID-19 pandemic, the integration of interpretable machine learning techniques has garnered significant attention, offering transparent and understandable insights crucial for informed clinical decision making.
Do We Really Need a Complex Agent System? Distill Embodied Agent into a Single Model
no code implementations • 6 Apr 2024 • Zhonghan Zhao, Ke Ma, Wenhao Chai, Xuan Wang, Kewei Chen, Dongxu Guo, Yanting Zhang, Hongwei Wang, Gaoang Wang
After distillation, embodied agents can complete complex, open-ended tasks without additional expert guidance, utilizing the performance and knowledge of a versatile MLM.
Block-Dominant Compressed Sensing for Near-Field Communications: Fundamentals, Solutions and Future Directions
no code implementations • 19 Mar 2024 • Liyang Lu, Ke Ma, Zhaocheng Wang
Near-field (NF) communications draw much attention in the context of extremely large-scale antenna arrays (ELAA).
A Robbins--Monro Sequence That Can Exploit Prior Information For Faster Convergence
no code implementations • 6 Jan 2024 • Siwei Liu, Ke Ma, Stephan M. Goetz
We propose a new method to improve the convergence speed of the Robbins-Monro algorithm by introducing prior information about the target point into the Robbins-Monro iteration.
Learning node representation via Motif Coarsening
1 code implementation • journal 2023 • Junyu Chen, Qianqian Xu, Zhiyong Yang, Ke Ma, Xiaochun Cao, Qingming Huang
For the motif-based node representation learning process, we propose a Motif Coarsening strategy for incorporating motif structure into the graph representation learning process.
Improving the Performance of R17 Type-II Codebook with Deep Learning
no code implementations • 13 Sep 2023 • Ke Ma, Yiliang Sang, Yang Ming, Jin Lian, Chang Tian, Zhaocheng Wang
The Type-II codebook in Release 17 (R17) exploits the angular-delay-domain partial reciprocity between uplink and downlink channels to select part of angular-delay-domain ports for measuring and feeding back the downlink channel state information (CSI), where the performance of existing deep learning enhanced CSI feedback methods is limited due to the deficiency of sparse structures.
SAM-Path: A Segment Anything Model for Semantic Segmentation in Digital Pathology
no code implementations • 12 Jul 2023 • Jingwei Zhang, Ke Ma, Saarthak Kapse, Joel Saltz, Maria Vakalopoulou, Prateek Prasanna, Dimitris Samaras
On these two datasets, the proposed additional pathology foundation model further achieves a relative improvement of 5. 07% to 5. 12% in Dice score and 4. 50% to 8. 48% in IOU.
Internal Contrastive Learning for Generalized Out-of-distribution Fault Diagnosis (GOOFD) Framework
no code implementations • 27 Jun 2023 • Xingyue Wang, Hanrong Zhang, Ke Ma, Shuting Tao, Peng Peng, Hongwei Wang
Additionally, a unified fault diagnosis method based on internal contrastive learning is put forward to underpin the proposed generalized framework.
Deep Learning Empowered Type-II Codebook: New Paradigm for Enhancing CSI Feedback
no code implementations • 14 May 2023 • Ke Ma, Yiliang Sang, Yang Ming, Jin Lian, Chang Tian, Zhaocheng Wang
In contrast to its counterpart in Release 16, the Type-II codebook in Release 17 (R17) exploits the angular-delay-domain partial reciprocity between uplink and downlink channels and selects part of angular-delay-domain ports for measuring and feeding back the downlink CSI, where the performance of the conventional deep learning methods is limited due to the deficiency of sparse structures.
An Ensemble Learning Approach for Exercise Detection in Type 1 Diabetes Patients
no code implementations • 11 May 2023 • Ke Ma, Hongkai Chen, Shan Lin
Artificial pancreas (AP) systems have been developed as a solution for type 1 diabetic patients to mimic the behavior of the pancreas and regulate blood glucose levels.
Improving Fast Adversarial Training with Prior-Guided Knowledge
no code implementations • 1 Apr 2023 • Xiaojun Jia, Yong Zhang, Xingxing Wei, Baoyuan Wu, Ke Ma, Jue Wang, Xiaochun Cao
This initialization is generated by using high-quality adversarial perturbations from the historical training process.
Prompt-MIL: Boosting Multi-Instance Learning Schemes via Task-specific Prompt Tuning
1 code implementation • 21 Mar 2023 • Jingwei Zhang, Saarthak Kapse, Ke Ma, Prateek Prasanna, Joel Saltz, Maria Vakalopoulou, Dimitris Samaras
Compared to conventional full fine-tuning approaches, we fine-tune less than 1. 3% of the parameters, yet achieve a relative improvement of 1. 29%-13. 61% in accuracy and 3. 22%-27. 18% in AUROC and reduce GPU memory consumption by 38%-45% while training 21%-27% faster.
OMSN and FAROS: OCTA Microstructure Segmentation Network and Fully Annotated Retinal OCTA Segmentation Dataset
no code implementations • 26 Dec 2022 • Peng Xiao, Xiaodong Hu, Ke Ma, Gengyuan Wang, Ziqing Feng, Yuancong Huang, Jin Yuan
The lack of efficient segmentation methods and fully-labeled datasets limits the comprehensive assessment of optical coherence tomography angiography (OCTA) microstructures like retinal vessel network (RVN) and foveal avascular zone (FAZ), which are of great value in ophthalmic and systematic diseases evaluation.
Precise Location Matching Improves Dense Contrastive Learning in Digital Pathology
1 code implementation • 23 Dec 2022 • Jingwei Zhang, Saarthak Kapse, Ke Ma, Prateek Prasanna, Maria Vakalopoulou, Joel Saltz, Dimitris Samaras
Our method outperforms previous dense matching methods by up to 7. 2% in average precision for detection and 5. 6% in average precision for instance segmentation tasks.
Recurrent Meta-Learning against Generalized Cold-start Problem in CTR Prediction
1 code implementation • Conference 2022 • Junyu Chen, Qianqian Xu, Zhiyong Yang, Ke Ma, Xiaochun Cao, Qingming Huang
To attack this problem, we propose a recursive meta-learning model with the user's behavior sequence prediction as a separate training task.
Exploring Inconsistent Knowledge Distillation for Object Detection with Data Augmentation
1 code implementation • 20 Sep 2022 • Jiawei Liang, Siyuan Liang, Aishan Liu, Ke Ma, Jingzhi Li, Xiaochun Cao
Specifically, we propose a sample-specific data augmentation to transfer the teacher model's ability in capturing distinct frequency components and suggest an adversarial feature augmentation to extract the teacher model's perceptions of non-robust features in the data.
A Tale of HodgeRank and Spectral Method: Target Attack Against Rank Aggregation Is the Fixed Point of Adversarial Game
1 code implementation • 13 Sep 2022 • Ke Ma, Qianqian Xu, Jinshan Zeng, Guorong Li, Xiaochun Cao, Qingming Huang
From the perspective of the dynamical system, the attack behavior with a target ranking list is a fixed point belonging to the composition of the adversary and the victim.
Prior-Guided Adversarial Initialization for Fast Adversarial Training
1 code implementation • 18 Jul 2022 • Xiaojun Jia, Yong Zhang, Xingxing Wei, Baoyuan Wu, Ke Ma, Jue Wang, Xiaochun Cao
Based on the observation, we propose a prior-guided FGSM initialization method to avoid overfitting after investigating several initialization strategies, improving the quality of the AEs during the whole training process.
 Adversarial Attack
Adversarial Attack
 Adversarial Attack on Video Classification
Adversarial Attack on Video Classification
Gigapixel Whole-Slide Images Classification using Locally Supervised Learning
1 code implementation • 17 Jul 2022 • Jingwei Zhang, Xin Zhang, Ke Ma, Rajarsi Gupta, Joel Saltz, Maria Vakalopoulou, Dimitris Samaras
Histopathology whole slide images (WSIs) play a very important role in clinical studies and serve as the gold standard for many cancer diagnoses.
LAS-AT: Adversarial Training with Learnable Attack Strategy
1 code implementation • CVPR 2022 • Xiaojun Jia, Yong Zhang, Baoyuan Wu, Ke Ma, Jue Wang, Xiaochun Cao
In this paper, we propose a novel framework for adversarial training by introducing the concept of "learnable attack strategy", dubbed LAS-AT, which learns to automatically produce attack strategies to improve the model robustness.
Visual attention analysis of pathologists examining whole slide images of Prostate cancer
no code implementations • 17 Feb 2022 • Souradeep Chakraborty, Ke Ma, Rajarsi Gupta, Beatrice Knudsen, Gregory J. Zelinsky, Joel H. Saltz, Dimitris Samaras
To quantify the relationship between a pathologist's attention and evidence for cancer in the WSI, we obtained tumor annotations from a genitourinary specialist.
Advancing COVID-19 Diagnosis with Privacy-Preserving Collaboration in Artificial Intelligence
1 code implementation • 18 Nov 2021 • Xiang Bai, Hanchen Wang, Liya Ma, Yongchao Xu, Jiefeng Gan, Ziwei Fan, Fan Yang, Ke Ma, Jiehua Yang, Song Bai, Chang Shu, Xinyu Zou, Renhao Huang, Changzheng Zhang, Xiaowu Liu, Dandan Tu, Chuou Xu, Wenqing Zhang, Xi Wang, Anguo Chen, Yu Zeng, Dehua Yang, Ming-Wei Wang, Nagaraj Holalkere, Neil J. Halin, Ihab R. Kamel, Jia Wu, Xuehua Peng, Xiang Wang, Jianbo Shao, Pattanasak Mongkolwat, Jianjun Zhang, Weiyang Liu, Michael Roberts, Zhongzhao Teng, Lucian Beer, Lorena Escudero Sanchez, Evis Sala, Daniel Rubin, Adrian Weller, Joan Lasenby, Chuangsheng Zheng, Jianming Wang, Zhen Li, Carola-Bibiane Schönlieb, Tian Xia
Artificial intelligence (AI) provides a promising substitution for streamlining COVID-19 diagnoses.
Learning Surface Parameterization for Document Image Unwarping
no code implementations • 29 Sep 2021 • Sagnik Das, Ke Ma, Zhixin Shu, Dimitris Samaras
We also demonstrate the usefulness of our system by applying it to document texture editing.
Efficient Semi-Discrete Optimal Transport Using the Maximum Relative Error between Distributions
no code implementations • 29 Sep 2021 • Huidong Liu, Ke Ma, Lei Zhou, Dimitris Samaras
If the \texttt{MRE} is smaller than 1, then every target point is guaranteed to have an area in the source distribution that is mapped to it.
Poisoning Attack against Estimating from Pairwise Comparisons
1 code implementation • 5 Jul 2021 • Ke Ma, Qianqian Xu, Jinshan Zeng, Xiaochun Cao, Qingming Huang
In this paper, to the best of our knowledge, we initiate the first systematic investigation of data poisoning attacks on pairwise ranking algorithms, which can be formalized as the dynamic and static games between the ranker and the attacker and can be modeled as certain kinds of integer programming problems.
A Joint Spatial and Magnification Based Attention Framework for Large Scale Histopathology Classification
no code implementations • CVPR 2021 • Jingwei Zhang, Ke Ma, John Van Arnam, Rajarsi Gupta, Joel Saltz, Maria Vakalopoulou, Dimitris Samaras
To tackle these problems, we propose a novel spatial and magnification based attention sampling strategy.
HAIR: Head-mounted AR Intention Recognition
no code implementations • 22 Feb 2021 • David Puljiz, BoWen Zhou, Ke Ma, Björn Hein
In this paper we propose an intention recognition system that is based purely on a portable head-mounted display.
 Intent Detection
Robotics
Human-Computer Interaction
Intent Detection
Robotics
Human-Computer Interaction
AdaSpring: Context-adaptive and Runtime-evolutionary Deep Model Compression for Mobile Applications
no code implementations • 28 Jan 2021 • Sicong Liu, Bin Guo, Ke Ma, Zhiwen Yu, Junzhao Du
There are many deep learning (e. g., DNN) powered mobile and wearable applications today continuously and unobtrusively sensing the ambient surroundings to enhance all aspects of human lives.
Deep Learning Assisted Calibrated Beam Training for Millimeter-Wave Communication Systems
1 code implementation • 8 Jan 2021 • Ke Ma, Dongxuan He, Hancun Sun, Zhaocheng Wang, Sheng Chen
To tackle this problem, the second scheme adopts long-short term memory (LSTM) network for tracking the movement of users and calibrating the beam direction according to the received signals of prior beam training, in order to enhance the robustness to noise.
On Stochastic Variance Reduced Gradient Method for Semidefinite Optimization
no code implementations • 1 Jan 2021 • Jinshan Zeng, Yixuan Zha, Ke Ma, Yuan YAO
In this paper, we fill this gap via exploiting a new semi-stochastic variant of the original SVRG with Option I adapted to the semidefinite optimization.
Intrinsic Decomposition of Document Images In-the-Wild
1 code implementation • 29 Nov 2020 • Sagnik Das, Hassan Ahmed Sial, Ke Ma, Ramon Baldrich, Maria Vanrell, Dimitris Samaras
However, document shadow or shading removal results still suffer because: (a) prior methods rely on uniformity of local color statistics, which limit their application on real-scenarios with complex document shapes and textures and; (b) synthetic or hybrid datasets with non-realistic, simulated lighting conditions are used to train the models.
Deep Learning Assisted mmWave Beam Prediction with Prior Low-frequency Information
no code implementations • 30 Oct 2020 • Ke Ma, Dongxuan He, Hancun Sun, Zhaocheng Wang
Huge overhead of beam training poses a significant challenge to mmWave communications.
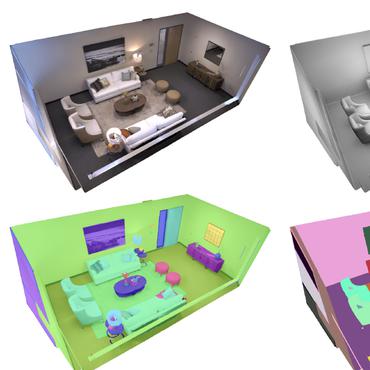
Attribute-guided image generation from layout
2 code implementations • 27 Aug 2020 • Ke Ma, Bo Zhao, Leonid Sigal
Also, the generated images from our model have higher resolution, object classification accuracy and consistency, as compared to the previous state-of-the-art.
Fast Stochastic Ordinal Embedding with Variance Reduction and Adaptive Step Size
no code implementations • 1 Dec 2019 • Ke Ma, Jinshan Zeng, Qianqian Xu, Xiaochun Cao, Wei Liu, Yuan YAO
Learning representation from relative similarity comparisons, often called ordinal embedding, gains rising attention in recent years.
Collaborative Preference Embedding against Sparse Labels
1 code implementation • ACM MM 2019 • Shilong Bao, Qianqian Xu, Ke Ma, Zhiyong Yang, Xiaochun Cao, Qingming Huang
From the margin theory point-of-view, we then propose a generalization enhancement scheme for sparse and insufficient labels via optimizing the margin distribution.
Less but Better: Generalization Enhancement of Ordinal Embedding via Distributional Margin
1 code implementation • 5 Dec 2018 • Ke Ma, Qianqian Xu, Zhiyong Yang, Xiaochun Cao
To address the issue of insufficient training samples, we propose a margin distribution learning paradigm for ordinal embedding, entitled Distributional Margin based Ordinal Embedding (\textit{DMOE}).
Robust Ordinal Embedding from Contaminated Relative Comparisons
1 code implementation • 5 Dec 2018 • Ke Ma, Qianqian Xu, Xiaochun Cao
Existing ordinal embedding methods usually follow a two-stage routine: outlier detection is first employed to pick out the inconsistent comparisons; then an embedding is learned from the clean data.
DocUNet: Document Image Unwarping via a Stacked U-Net
1 code implementation • CVPR 2018 • Ke Ma, Zhixin Shu, Xue Bai, Jue Wang, Dimitris Samaras
The network is trained on this dataset with various data augmentations to improve its generalization ability.
 Ranked #4 on
SSIM
on DocUNet
(using extra training data)
Ranked #4 on
SSIM
on DocUNet
(using extra training data)
Stochastic Non-convex Ordinal Embedding with Stabilized Barzilai-Borwein Step Size
1 code implementation • 17 Nov 2017 • Ke Ma, Jinshan Zeng, Jiechao Xiong, Qianqian Xu, Xiaochun Cao, Wei Liu, Yuan YAO
Learning representation from relative similarity comparisons, often called ordinal embedding, gains rising attention in recent years.