Search Results for author: Leman Akoglu
Found 50 papers, 28 papers with code
End-To-End Self-tuning Self-supervised Time Series Anomaly Detection
no code implementations • 3 Apr 2024 • Boje Deforce, Meng-Chieh Lee, Bart Baesens, Estefanía Serral Asensio, Jaemin Yoo, Leman Akoglu
A two-fold challenge for TSAD is a versatile and unsupervised model that can detect various different types of time series anomalies (spikes, discontinuities, trend shifts, etc.)
On the Detection of Reviewer-Author Collusion Rings From Paper Bidding
1 code implementation • 12 Feb 2024 • Steven Jecmen, Nihar B. Shah, Fei Fang, Leman Akoglu
A major threat to the peer-review systems of computer science conferences is the existence of "collusion rings" between reviewers.
Descriptive Kernel Convolution Network with Improved Random Walk Kernel
1 code implementation • 8 Feb 2024 • Meng-Chieh Lee, Lingxiao Zhao, Leman Akoglu
In this paper, we first revisit the RWK and its current usage in KCNs, revealing several shortcomings of the existing designs, and propose an improved graph kernel RWK+, by introducing color-matching random walks and deriving its efficient computation.
Improving and Unifying Discrete&Continuous-time Discrete Denoising Diffusion
2 code implementations • 6 Feb 2024 • Lingxiao Zhao, Xueying Ding, Lijun Yu, Leman Akoglu
Discrete diffusion models have seen a surge of attention with applications on naturally discrete data such as language and graphs.
Pard: Permutation-Invariant Autoregressive Diffusion for Graph Generation
1 code implementation • 6 Feb 2024 • Lingxiao Zhao, Xueying Ding, Leman Akoglu
Current graph diffusion models generate graphs in a one-shot fashion, but they require extra features and thousands of denoising steps to achieve optimal performance.
ADAMM: Anomaly Detection of Attributed Multi-graphs with Metadata: A Unified Neural Network Approach
1 code implementation • 13 Nov 2023 • Konstantinos Sotiropoulos, Lingxiao Zhao, Pierre Jinghong Liang, Leman Akoglu
Given a complex graph database of node- and edge-attributed multi-graphs as well as associated metadata for each graph, how can we spot the anomalous instances?
Self-Supervision for Tackling Unsupervised Anomaly Detection: Pitfalls and Opportunities
no code implementations • 28 Aug 2023 • Leman Akoglu, Jaemin Yoo
Self-supervised learning (SSL) is a growing torrent that has recently transformed machine learning and its many real world applications, by learning on massive amounts of unlabeled data via self-generated supervisory signals.
Fast Unsupervised Deep Outlier Model Selection with Hypernetworks
no code implementations • 20 Jul 2023 • Xueying Ding, Yue Zhao, Leman Akoglu
Outlier detection (OD) finds many applications with a rich literature of numerous techniques.
DSV: An Alignment Validation Loss for Self-supervised Outlier Model Selection
1 code implementation • 13 Jul 2023 • Jaemin Yoo, Yue Zhao, Lingxiao Zhao, Leman Akoglu
DSV captures the alignment between an augmentation function and the anomaly-generating mechanism with surrogate losses, which approximate the discordance and separability of test data, respectively.
End-to-End Augmentation Hyperparameter Tuning for Self-Supervised Anomaly Detection
no code implementations • 21 Jun 2023 • Jaemin Yoo, Lingxiao Zhao, Leman Akoglu
The first is a new unsupervised validation loss that quantifies the alignment between the augmented training data and the (unlabeled) test data.
From Explanation to Action: An End-to-End Human-in-the-loop Framework for Anomaly Reasoning and Management
no code implementations • 6 Apr 2023 • Xueying Ding, Nikita Seleznev, Senthil Kumar, C. Bayan Bruss, Leman Akoglu
Anomalies are often indicators of malfunction or inefficiency in various systems such as manufacturing, healthcare, finance, surveillance, to name a few.
Unsupervised Machine Learning for Explainable Health Care Fraud Detection
no code implementations • 5 Nov 2022 • Shubhranshu Shekhar, Jetson Leder-Luis, Leman Akoglu
The US federal government spends more than a trillion dollars per year on health care, largely provided by private third parties and reimbursed by the government.
Toward Unsupervised Outlier Model Selection
1 code implementation • 3 Nov 2022 • Yue Zhao, Sean Zhang, Leman Akoglu
At its core, ELECT is based on meta-learning; transferring prior knowledge (e. g. model performance) on historical datasets that are similar to the new one to facilitate UOMS.
A Practical, Progressively-Expressive GNN
1 code implementation • 18 Oct 2022 • Lingxiao Zhao, Louis Härtel, Neil Shah, Leman Akoglu
Our model is practical and progressively-expressive, increasing in power with k and c. We demonstrate effectiveness on several benchmark datasets, achieving several state-of-the-art results with runtime and memory usage applicable to practical graphs.
Graph Anomaly Detection with Unsupervised GNNs
1 code implementation • 18 Oct 2022 • Lingxiao Zhao, Saurabh Sawlani, Arvind Srinivasan, Leman Akoglu
This work aims to fill two gaps in the literature: We (1) design GLAM, an end-to-end graph-level anomaly detection model based on GNNs, and (2) focus on unsupervised model selection, which is notoriously hard due to lack of any labels, yet especially critical for deep NN based models with a long list of hyper-parameters.
D.MCA: Outlier Detection with Explicit Micro-Cluster Assignments
1 code implementation • 15 Oct 2022 • Shuli Jiang, Robson Leonardo Ferreira Cordeiro, Leman Akoglu
How can we perform both tasks in-house, i. e., without any post-hoc processing, so that both detection and assignment can benefit simultaneously from each other?
Hyperparameter Optimization for Unsupervised Outlier Detection
no code implementations • 24 Aug 2022 • Yue Zhao, Leman Akoglu
Given an unsupervised outlier detection (OD) algorithm, how can we optimize its hyperparameter(s) (HP) on a new dataset, without any labels?
Data Augmentation is a Hyperparameter: Cherry-picked Self-Supervision for Unsupervised Anomaly Detection is Creating the Illusion of Success
1 code implementation • 16 Aug 2022 • Jaemin Yoo, Tiancheng Zhao, Leman Akoglu
Self-supervised learning (SSL) has emerged as a promising alternative to create supervisory signals to real-world problems, avoiding the extensive cost of manual labeling.
Hyperparameter Sensitivity in Deep Outlier Detection: Analysis and a Scalable Hyper-Ensemble Solution
1 code implementation • 15 Jun 2022 • Xueying Ding, Lingxiao Zhao, Leman Akoglu
Outlier detection (OD) literature exhibits numerous algorithms as it applies to diverse domains.
Automatic Unsupervised Outlier Model Selection
no code implementations • NeurIPS 2021 • Yue Zhao, Ryan Rossi, Leman Akoglu
Given an unsupervised outlier detection task on a new dataset, how can we automatically select a good outlier detection algorithm and its hyperparameter(s) (collectively called a model)?
Benefit-aware Early Prediction of Health Outcomes on Multivariate EEG Time Series
no code implementations • 11 Nov 2021 • Shubhranshu Shekhar, Dhivya Eswaran, Bryan Hooi, Jonathan Elmer, Christos Faloutsos, Leman Akoglu
Given a cardiac-arrest patient being monitored in the ICU (intensive care unit) for brain activity, how can we predict their health outcomes as early as possible?
C-AllOut: Catching & Calling Outliers by Type
no code implementations • 13 Oct 2021 • Guilherme D. F. Silva, Leman Akoglu, Robson L. F. Cordeiro
It is parameter-free and scalable, besides working only with pairwise similarities (or distances) when it is needed.
Fast Attributed Graph Embedding via Density of States
1 code implementation • 11 Oct 2021 • Saurabh Sawlani, Lingxiao Zhao, Leman Akoglu
We propose A-DOGE, for Attributed DOS-based Graph Embedding, based on density of states (DOS, a. k. a.
From Stars to Subgraphs: Uplifting Any GNN with Local Structure Awareness
2 code implementations • ICLR 2022 • Lingxiao Zhao, Wei Jin, Leman Akoglu, Neil Shah
We choose the subgraph encoder to be a GNN (mainly MPNNs, considering scalability) to design a general framework that serves as a wrapper to up-lift any GNN.
 Ranked #16 on
Graph Property Prediction
on ogbg-molpcba
Ranked #16 on
Graph Property Prediction
on ogbg-molpcba
Connecting Graph Convolution and Graph PCA
no code implementations • 29 Sep 2021 • Lingxiao Zhao, Leman Akoglu
Based on this connection, the GCN architecture, shaped by stacking graph convolution layers, shares a close relationship with stacking GPCA.
A Comprehensive Survey on Graph Anomaly Detection with Deep Learning
1 code implementation • 14 Jun 2021 • Xiaoxiao Ma, Jia Wu, Shan Xue, Jian Yang, Chuan Zhou, Quan Z. Sheng, Hui Xiong, Leman Akoglu
In this survey, we aim to provide a systematic and comprehensive review of the contemporary deep learning techniques for graph anomaly detection.
Anomaly Mining -- Past, Present and Future
no code implementations • 21 May 2021 • Leman Akoglu
Anomaly mining is an important problem that finds numerous applications in various real world domains such as environmental monitoring, cybersecurity, finance, healthcare and medicine, to name a few.
A Large-scale Study on Unsupervised Outlier Model Selection: Do Internal Strategies Suffice?
1 code implementation • 3 Apr 2021 • Martin Q. Ma, Yue Zhao, Xiaorong Zhang, Leman Akoglu
These so-called internal strategies solely rely on the input data (without labels) and the output (outlier scores) of the candidate models.
On Using Classification Datasets to Evaluate Graph-Level Outlier Detection: Peculiar Observations and New Insights
1 code implementation • 23 Dec 2020 • Lingxiao Zhao, Leman Akoglu
We carefully study the graph embedding space produced by propagation based models and find two driving factors: (1) disparity between within-class densities which is amplified by propagation, and (2)overlapping support (mixing of embeddings) across classes.
FairOD: Fairness-aware Outlier Detection
1 code implementation • 5 Dec 2020 • Shubhranshu Shekhar, Neil Shah, Leman Akoglu
Fairness and Outlier Detection (OD) are closely related, as it is exactly the goal of OD to spot rare, minority samples in a given population.
AutoAudit: Mining Accounting and Time-Evolving Graphs
1 code implementation • 1 Nov 2020 • Meng-Chieh Lee, Yue Zhao, Aluna Wang, Pierre Jinghong Liang, Leman Akoglu, Vincent S. Tseng, Christos Faloutsos
How can we spot money laundering in large-scale graph-like accounting datasets?
Social and Information Networks
Anomaly Detection in Large Labeled Multi-Graph Databases
no code implementations • 7 Oct 2020 • Hung T. Nguyen, Pierre J. Liang, Leman Akoglu
Within a large database G containing graphs with labeled nodes and directed, multi-edges; how can we detect the anomalous graphs?
Automating Outlier Detection via Meta-Learning
1 code implementation • 22 Sep 2020 • Yue Zhao, Ryan A. Rossi, Leman Akoglu
Given an unsupervised outlier detection (OD) task on a new dataset, how can we automatically select a good outlier detection method and its hyperparameter(s) (collectively called a model)?
Connecting Graph Convolutional Networks and Graph-Regularized PCA
no code implementations • 22 Jun 2020 • Lingxiao Zhao, Leman Akoglu
Based on this connection, GCN architecture, shaped by stacking graph convolution layers, shares a close relationship with stacking GPCA.
Beyond Homophily in Graph Neural Networks: Current Limitations and Effective Designs
4 code implementations • NeurIPS 2020 • Jiong Zhu, Yujun Yan, Lingxiao Zhao, Mark Heimann, Leman Akoglu, Danai Koutra
We investigate the representation power of graph neural networks in the semi-supervised node classification task under heterophily or low homophily, i. e., in networks where connected nodes may have different class labels and dissimilar features.
SUOD: Accelerating Large-Scale Unsupervised Heterogeneous Outlier Detection
1 code implementation • 11 Mar 2020 • Yue Zhao, Xiyang Hu, Cheng Cheng, Cong Wang, Changlin Wan, Wen Wang, Jianing Yang, Haoping Bai, Zheng Li, Cao Xiao, Yunlong Wang, Zhi Qiao, Jimeng Sun, Leman Akoglu
Outlier detection (OD) is a key machine learning (ML) task for identifying abnormal objects from general samples with numerous high-stake applications including fraud detection and intrusion detection.
Coverage-based Outlier Explanation
no code implementations • 6 Nov 2019 • Yue Wu, Leman Akoglu, Ian Davidson
Existing algorithms are primarily focused on detection, that is the identification of outliers in a given dataset.
PairNorm: Tackling Oversmoothing in GNNs
1 code implementation • ICLR 2020 • Lingxiao Zhao, Leman Akoglu
The performance of graph neural nets (GNNs) is known to gradually decrease with increasing number of layers.
A Quest for Structure: Jointly Learning the Graph Structure and Semi-Supervised Classification
1 code implementation • 26 Sep 2019 • Xuan Wu, Lingxiao Zhao, Leman Akoglu
As such, PG-learn is a carefully-designed hybrid of random and adaptive search.
Statistical Analysis of Nearest Neighbor Methods for Anomaly Detection
1 code implementation • NeurIPS 2019 • Xiaoyi Gu, Leman Akoglu, Alessandro Rinaldo
Nearest-neighbor (NN) procedures are well studied and widely used in both supervised and unsupervised learning problems.
Continual Rare-Class Recognition with Emerging Novel Subclasses
1 code implementation • 28 Jun 2019 • Hung Nguyen, Xuejian Wang, Leman Akoglu
We introduce RaRecognize, which (i) estimates a general decision boundary between the rare and the majority class, (ii) learns to recognize individual rare subclasses that exist within the training data, as well as (iii) flags instances from previously unseen rare subclasses as newly emerging.
Incorporating Privileged Information to Unsupervised Anomaly Detection
no code implementations • 6 May 2018 • Shubhranshu Shekhar, Leman Akoglu
We introduce a new unsupervised anomaly detection ensemble called SPI which can harness privileged information - data available only for training examples but not for (future) test examples.
Explaining Anomalies in Groups with Characterizing Subspace Rules
1 code implementation • 20 Aug 2017 • Meghanath Macha, Leman Akoglu
We consider a complementary problem that has a much sparser literature: anomaly description.
Sequential Ensemble Learning for Outlier Detection: A Bias-Variance Perspective
no code implementations • 18 Sep 2016 • Shebuti Rayana, Wen Zhong, Leman Akoglu
In this work, we design a new ensemble approach for outlier detection in multi-dimensional point data, which provides improved accuracy by reducing error through both bias and variance.
BIRDNEST: Bayesian Inference for Ratings-Fraud Detection
no code implementations • 19 Nov 2015 • Bryan Hooi, Neil Shah, Alex Beutel, Stephan Gunnemann, Leman Akoglu, Mohit Kumar, Disha Makhija, Christos Faloutsos
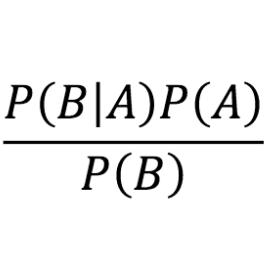
To combine these 2 approaches, we formulate our Bayesian Inference for Rating Data (BIRD) model, a flexible Bayesian model of user rating behavior.
Robust Semi-Supervised Classification for Multi-Relational Graphs
no code implementations • 19 Oct 2015 • Junting Ye, Leman Akoglu
We provide a careful analysis of the inferred weights, based on which we devise an algorithm that filters out irrelevant and noisy graphs and produces weights proportional to the informativeness of the remaining graphs.
Less is More: Building Selective Anomaly Ensembles
no code implementations • 8 Jan 2015 • Shebuti Rayana, Leman Akoglu
In this work, we tap into this gap and propose a new ensemble approach for anomaly mining, with application to event detection in temporal graphs.
Graph-based Anomaly Detection and Description: A Survey
1 code implementation • 18 Apr 2014 • Leman Akoglu, Hanghang Tong, Danai Koutra
This survey aims to provide a general, comprehensive, and structured overview of the state-of-the-art methods for anomaly detection in data represented as graphs.
Social and Information Networks Cryptography and Security
Want a Good Answer? Ask a Good Question First!
no code implementations • 27 Nov 2013 • Yuan Yao, Hanghang Tong, Tao Xie, Leman Akoglu, Feng Xu, Jian Lu
Community Question Answering (CQA) websites have become valuable repositories which host a massive volume of human knowledge.