Search Results for author: Gorka Abad
Found 5 papers, 1 papers with code
Time-Distributed Backdoor Attacks on Federated Spiking Learning
no code implementations • 5 Feb 2024 • Gorka Abad, Stjepan Picek, Aitor Urbieta
Then, we evaluate the transferability of known FL attack methods to SNNs, finding that these lead to suboptimal attack performance.
Tabdoor: Backdoor Vulnerabilities in Transformer-based Neural Networks for Tabular Data
no code implementations • 13 Nov 2023 • Bart Pleiter, Behrad Tajalli, Stefanos Koffas, Gorka Abad, Jing Xu, Martha Larson, Stjepan Picek
Deep Neural Networks (DNNs) have shown great promise in various domains.
Rethinking the Trigger-injecting Position in Graph Backdoor Attack
no code implementations • 5 Apr 2023 • Jing Xu, Gorka Abad, Stjepan Picek
There is no work analyzing and explaining the backdoor attack performance when injecting triggers into the most important or least important area in the sample, which we refer to as trigger-injecting strategies MIAS and LIAS, respectively.
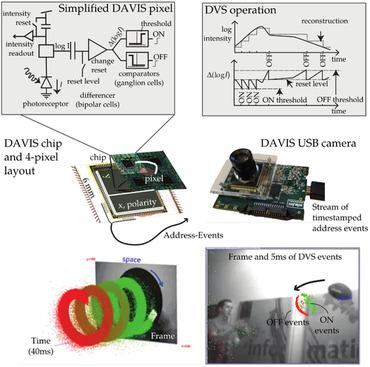
Sneaky Spikes: Uncovering Stealthy Backdoor Attacks in Spiking Neural Networks with Neuromorphic Data
1 code implementation • 13 Feb 2023 • Gorka Abad, Oguzhan Ersoy, Stjepan Picek, Aitor Urbieta
Deep neural networks (DNNs) have demonstrated remarkable performance across various tasks, including image and speech recognition.
 Ranked #1 on
Image Classification
on DVS128 Gesture
Ranked #1 on
Image Classification
on DVS128 Gesture
SoK: A Systematic Evaluation of Backdoor Trigger Characteristics in Image Classification
no code implementations • 3 Feb 2023 • Gorka Abad, Jing Xu, Stefanos Koffas, Behrad Tajalli, Stjepan Picek, Mauro Conti
Nevertheless, it is vulnerable to backdoor attacks that modify the training set to embed a secret functionality in the trained model.