Search Results for author: Chen Cao
Found 15 papers, 2 papers with code
URHand: Universal Relightable Hands
no code implementations • 10 Jan 2024 • Zhaoxi Chen, Gyeongsik Moon, Kaiwen Guo, Chen Cao, Stanislav Pidhorskyi, Tomas Simon, Rohan Joshi, Yuan Dong, Yichen Xu, Bernardo Pires, He Wen, Lucas Evans, Bo Peng, Julia Buffalini, Autumn Trimble, Kevyn McPhail, Melissa Schoeller, Shoou-I Yu, Javier Romero, Michael Zollhöfer, Yaser Sheikh, Ziwei Liu, Shunsuke Saito
To simplify the personalization process while retaining photorealism, we build a powerful universal relightable prior based on neural relighting from multi-view images of hands captured in a light stage with hundreds of identities.
A Local Appearance Model for Volumetric Capture of Diverse Hairstyle
no code implementations • 14 Dec 2023 • Ziyan Wang, Giljoo Nam, Aljaz Bozic, Chen Cao, Jason Saragih, Michael Zollhoefer, Jessica Hodgins
In this paper, we present a novel method for creating high-fidelity avatars with diverse hairstyles.
Elucidating STEM Concepts through Generative AI: A Multi-modal Exploration of Analogical Reasoning
no code implementations • 21 Aug 2023 • Chen Cao, Zijian Ding, Gyeong-Geon Lee, Jiajun Jiao, Jionghao Lin, Xiaoming Zhai
Our study demonstrates the potential of applying large language models to educational practice on STEM subjects.
A Case Study of Large Language Models (ChatGPT and CodeBERT) for Security-Oriented Code Analysis
1 code implementation • 24 Jul 2023 • Zhilong Wang, Lan Zhang, Chen Cao, Nanqing Luo, Peng Liu
LLMs can be used on code analysis tasks like code review, vulnerabilities analysis and etc.
 Ranked #3 on
Code Generation
on MBPP
Ranked #3 on
Code Generation
on MBPP
Leveraging Large Language Model and Story-Based Gamification in Intelligent Tutoring System to Scaffold Introductory Programming Courses: A Design-Based Research Study
no code implementations • 25 Feb 2023 • Chen Cao
Programming skills are rapidly becoming essential for many educational paths and career opportunities.
Which Features are Learned by CodeBert: An Empirical Study of the BERT-based Source Code Representation Learning
no code implementations • 20 Jan 2023 • Lan Zhang, Chen Cao, Zhilong Wang, Peng Liu
The Bidirectional Encoder Representations from Transformers (BERT) were proposed in the natural language process (NLP) and shows promising results.
NeuWigs: A Neural Dynamic Model for Volumetric Hair Capture and Animation
no code implementations • CVPR 2023 • Ziyan Wang, Giljoo Nam, Tuur Stuyck, Stephen Lombardi, Chen Cao, Jason Saragih, Michael Zollhoefer, Jessica Hodgins, Christoph Lassner
The capture and animation of human hair are two of the major challenges in the creation of realistic avatars for the virtual reality.
High-fidelity Face Tracking for AR/VR via Deep Lighting Adaptation
no code implementations • CVPR 2021 • Lele Chen, Chen Cao, Fernando de la Torre, Jason Saragih, Chenliang Xu, Yaser Sheikh
This paper addresses previous limitations by learning a deep learning lighting model, that in combination with a high-quality 3D face tracking algorithm, provides a method for subtle and robust facial motion transfer from a regular video to a 3D photo-realistic avatar.
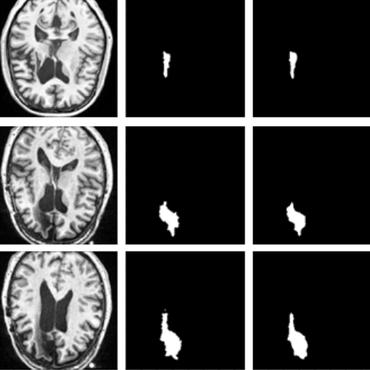
Automated Segmentation of Brain Gray Matter Nuclei on Quantitative Susceptibility Mapping Using Deep Convolutional Neural Network
no code implementations • 3 Aug 2020 • Chao Chai, Pengchong Qiao, Bin Zhao, Huiying Wang, Guohua Liu, Hong Wu, E Mark Haacke, Wen Shen, Chen Cao, Xinchen Ye, Zhiyang Liu, Shuang Xia
Abnormal iron accumulation in the brain subcortical nuclei has been reported to be correlated to various neurodegenerative diseases, which can be measured through the magnetic susceptibility from the quantitative susceptibility mapping (QSM).
Fully Convolutional Mesh Autoencoder using Efficient Spatially Varying Kernels
1 code implementation • NeurIPS 2020 • Yi Zhou, Chenglei Wu, Zimo Li, Chen Cao, Yuting Ye, Jason Saragih, Hao Li, Yaser Sheikh
Learning latent representations of registered meshes is useful for many 3D tasks.
Automatic acute ischemic stroke lesion segmentation using semi-supervised learning
no code implementations • 10 Aug 2019 • Bin Zhao, Shuxue Ding, Hong Wu, Guohua Liu, Chen Cao, Song Jin, Zhiyang Liu
By using a large number of weakly labeled subjects and a small number of fully labeled subjects, our proposed method is able to accurately detect and segment the AIS lesions.
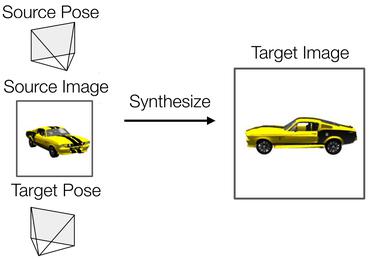
3D Guided Fine-Grained Face Manipulation
no code implementations • CVPR 2019 • Zhenglin Geng, Chen Cao, Sergey Tulyakov
This is achieved by first fitting a 3D face model and then disentangling the face into a texture and a shape.
Towards Clinical Diagnosis: Automated Stroke Lesion Segmentation on Multimodal MR Image Using Convolutional Neural Network
no code implementations • 5 Mar 2018 • Zhiyang Liu, Chen Cao, Shuxue Ding, Tong Han, Hong Wu, Sheng Liu
The patient with ischemic stroke can benefit most from the earliest possible definitive diagnosis.
Hey, you, keep away from my device: remotely implanting a virus expeller to defeat Mirai on IoT devices
no code implementations • 19 Jun 2017 • Chen Cao, Le Guan, Peng Liu, Neng Gao, Jingqiang Lin, Ji Xiang
In particular, at a negotiated time slot, a customer is required to reboot the compromised device, then a "white" Mirai operated by the manufacturer breaks into the clean-state IoT devices immediately.
Cryptography and Security
Context-aware System Service Call-oriented Symbolic Execution of Android Framework with Application to Exploit Generation
no code implementations • 2 Nov 2016 • Lannan Luo, Qiang Zeng, Chen Cao, Kai Chen, Jian Liu, Limin Liu, Neng Gao, Min Yang, Xinyu Xing, Peng Liu
We present novel ideas and techniques to resolve the challenges, and have built the first system for symbolic execution of Android Framework.
Cryptography and Security Software Engineering