Search Results for author: Xiaojiao Chen
Found 2 papers, 0 papers with code
GhostVec: A New Threat to Speaker Privacy of End-to-End Speech Recognition System
no code implementations • 17 Nov 2023 • Xiaojiao Chen, Sheng Li, Jiyi Li, Hao Huang, Yang Cao, Liang He
This paper demonstrates that an attacker can extract speaker information by querying speaker-adapted speech recognition (ASR) systems.
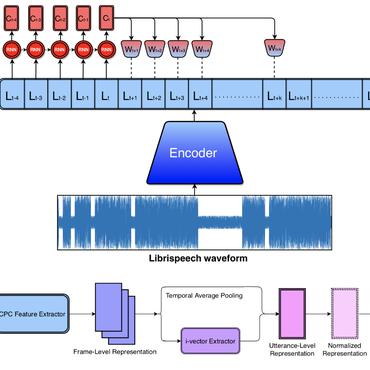
Reprogramming Self-supervised Learning-based Speech Representations for Speaker Anonymization
no code implementations • 17 Nov 2023 • Xiaojiao Chen, Sheng Li, Jiyi Li, Hao Huang, Yang Cao, Liang He
Current speaker anonymization methods, especially with self-supervised learning (SSL) models, require massive computational resources when hiding speaker identity.