Search Results for author: Jingze Lu
Found 7 papers, 0 papers with code
Enhancing Spoofing Speech Detection Using Rhythm Information
no code implementations • 18 Oct 2023 • Jingze Lu, Yuxiang Zhang, Wenchao Wang, Zengqiang Shang, Pengyuan Zhang
Current spoofing speech detection systems need more convincing evidence.
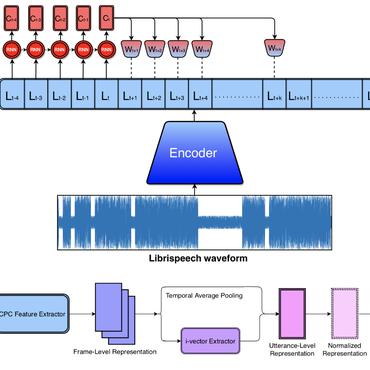
Synthetic Speech Detection Based on Temporal Consistency and Distribution of Speaker Features
no code implementations • 29 Sep 2023 • Yuxiang Zhang, Zhuo Li, Jingze Lu, Wenchao Wang, Pengyuan Zhang
Based on these analyzes, an SSD method based on temporal consistency and distribution of speaker features is proposed.
The Impact of Silence on Speech Anti-Spoofing
no code implementations • 21 Sep 2023 • Yuxiang Zhang, Zhuo Li, Jingze Lu, Hua Hua, Wenchao Wang, Pengyuan Zhang
First, the reasons for the impact are explored, including the proportion of silence duration and the content of silence.
One-Class Knowledge Distillation for Spoofing Speech Detection
no code implementations • 15 Sep 2023 • Jingze Lu, Yuxiang Zhang, Wenchao Wang, Zengqiang Shang, Pengyuan Zhang
The detection of spoofing speech generated by unseen algorithms remains an unresolved challenge.
Improving Short Utterance Anti-Spoofing with AASIST2
no code implementations • 15 Sep 2023 • Yuxiang Zhang, Jingze Lu, Zengqiang Shang, Wenchao Wang, Pengyuan Zhang
The modified Res2Net blocks can extract multi-scale features and improve the detection performance for speech of different durations, thus improving the short utterance evaluation performance.
Progressive Sub-Graph Clustering Algorithm for Semi-Supervised Domain Adaptation Speaker Verification
no code implementations • 22 May 2023 • Zhuo Li, Jingze Lu, Zhenduo Zhao, Wenchao Wang, Pengyuan Zhang
Utilizing the large-scale unlabeled data from the target domain via pseudo-label clustering algorithms is an important approach for addressing domain adaptation problems in speaker verification tasks.
Deepfake Detection System for the ADD Challenge Track 3.2 Based on Score Fusion
no code implementations • 13 Oct 2022 • Yuxiang Zhang, Jingze Lu, Xingming Wang, Zhuo Li, Runqiu Xiao, Wenchao Wang, Ming Li, Pengyuan Zhang
The overfitting of the model to the training set leads to extreme values of the scores and low correlation of the score distributions, which makes score fusion difficult.