Search Results for author: Yong Huang
Found 20 papers, 3 papers with code
Hierarchical sparse Bayesian learning: theory and application for inferring structural damage from incomplete modal data
no code implementations • 21 Mar 2015 • Yong Huang, James L. Beck
In this paper, we improve the theory of our previously proposed sparse Bayesian learning approach by eliminating an approximation and, more importantly, incorporating a constraint on stiffness increases.
Robust Bayesian compressive sensing with data loss recovery for structural health monitoring signals
no code implementations • 28 Mar 2015 • Yong Huang, James L. Beck, Stephen Wu, Hui Li
The application of compressive sensing (CS) to structural health monitoring is an emerging research topic.
Bayesian System Identification based on Hierarchical Sparse Bayesian Learning and Gibbs Sampling with Application to Structural Damage Assessment
no code implementations • 13 Jan 2017 • Yong Huang, James L. Beck, Hui Li
The focus in this paper is Bayesian system identification based on noisy incomplete modal data where we can impose spatially-sparse stiffness changes when updating a structural model.
Greedy Graph Searching for Vascular Tracking in Angiographic Image Sequences
no code implementations • 25 May 2018 • Huihui Fang, Jian Yang, Jianjun Zhu, Danni Ai, Yong Huang, Yurong Jiang, Hong Song, Yongtian Wang
The vascular branch was described using a vascular centerline extraction method with multi-probability fusion-based topology optimization.
Learning Structural Graph Layouts and 3D Shapes for Long Span Bridges 3D Reconstruction
no code implementations • 8 Jul 2019 • Fangqiao Hu, Jin Zhao, Yong Huang, Hui Li
Considering the prior human knowledge that these structures are in conformity to regular spatial layouts in terms of components, a learning-based topology-aware 3D reconstruction method which can obtain high-level structural graph layouts and low-level 3D shapes from images is proposed in this paper.
Recovering compressed images for automatic crack segmentation using generative models
no code implementations • 6 Mar 2020 • Yong Huang, Haoyu Zhang, Hui Li, Stephen Wu
We develop a recovery framework for automatic crack segmentation of compressed crack images based on this new CS method and demonstrate the remarkable performance of the method taking advantage of the strong capability of generative models to capture the necessary features required in the crack segmentation task even the backgrounds of the generated images are not well reconstructed.
A Multi-Modal and Multitask Benchmark in the Clinical Domain
no code implementations • 1 Jan 2021 • Yong Huang, Edgar Mariano Marroquin, Volodymyr Kuleshov
Here, we introduce Multi-Modal Multitask MIMIC-III (M3) — a dataset and benchmark for evaluating machine learning algorithms in the healthcare domain.
Towards Cross-Modal Forgery Detection and Localization on Live Surveillance Videos
no code implementations • 4 Jan 2021 • Yong Huang, Xiang Li, Wei Wang, Tao Jiang, Qian Zhang
Traditional video forensics approaches can detect and localize forgery traces in each video frame using computationally-expensive spatial-temporal analysis, while falling short in real-time verification of live video feeds.
 Time Series Analysis
Time Series Analysis
 Video Forensics
Cryptography and Security
Video Forensics
Cryptography and Security
LNSMM: Eye Gaze Estimation With Local Network Share Multiview Multitask
no code implementations • 18 Jan 2021 • Yong Huang, Ben Chen, Daiming Qu
Eye gaze estimation has become increasingly significant in computer vision. In this paper, we systematically study the mainstream of eye gaze estimation methods, propose a novel methodology to estimate eye gaze points and eye gaze directions simultaneously. First, we construct a local sharing network for feature extraction of gaze points and gaze directions estimation, which can reduce network computational parameters and converge quickly;Second, we propose a Multiview Multitask Learning (MTL) framework, for gaze directions, a coplanar constraint is proposed for the left and right eyes, for gaze points, three views data input indirectly introduces eye position information, a cross-view pooling module is designed, propose joint loss which handle both gaze points and gaze directions estimation. Eventually, we collect a dataset to use of gaze points, which have three views to exist public dataset. The experiment show our method is state-of-the-art the current mainstream methods on two indicators of gaze points and gaze directions.
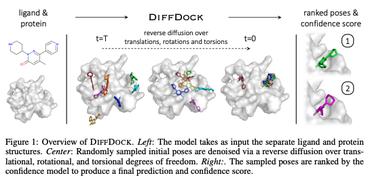
ResAtom System: Protein and Ligand Affinity Prediction Model Based on Deep Learning
no code implementations • 17 Apr 2021 • Yeji Wang, Shuo Wu, Yanwen Duan, Yong Huang
At the same time, we evaluated the performance of a variety of existing scoring functions in combination with ResAtom-Score in the absence of experimentally-determined conformations.
A Point Cloud-Based Deep Learning Strategy for Protein-Ligand Binding Affinity Prediction
no code implementations • 9 Jul 2021 • Yeji Wang, Shuo Wu, Yanwen Duan, Yong Huang
These results suggest that point clouds derived from the PDBbind datasets are useful to evaluate the performance of 3D point clouds-centered deep learning algorithms, which could learn critical protein-ligand interactions from natural evolution or medicinal chemistry and have wide applications in studying protein-ligand interactions.
Forgery Attack Detection in Surveillance Video Streams Using Wi-Fi Channel State Information
no code implementations • 24 Jan 2022 • Yong Huang, Xiang Li, Wei Wang, Tao Jiang, Qian Zhang
The cybersecurity breaches expose surveillance video streams to forgery attacks, under which authentic streams are falsified to hide unauthorized activities.
Parallel Fourier Ptychography reconstruction
no code implementations • 4 Mar 2022 • Guocheng Zhou, Shaohui Zhang, Yao Hu, Lei Cao, Yong Huang, Qun Hao
Fourier ptychography has attracted a wide range of focus for its ability of large space-bandwidth-produce, and quantative phase measurement.
Explored An Effective Methodology for Fine-Grained Snake Recognition
1 code implementation • 24 Jul 2022 • Yong Huang, Aderon Huang, Wei Zhu, Yanming Fang, Jinghua Feng
Then, in order to take full advantage of unlabeled datasets, we use self-supervised learning and supervised learning joint training to provide pre-trained model.
AI vs. Human -- Differentiation Analysis of Scientific Content Generation
no code implementations • 24 Jan 2023 • Yongqiang Ma, Jiawei Liu, Fan Yi, Qikai Cheng, Yong Huang, Wei Lu, Xiaozhong Liu
We find that there exists a "writing style" gap between AI-generated scientific text and human-written scientific text.
Low-Resource Multi-Granularity Academic Function Recognition Based on Multiple Prompt Knowledge
no code implementations • 5 May 2023 • Jiawei Liu, Zi Xiong, Yi Jiang, Yongqiang Ma, Wei Lu, Yong Huang, Qikai Cheng
Inspired by recent advancement in prompt learning, in this paper, we propose the Mix Prompt Tuning (MPT), which is a semi-supervised method to alleviate the dependence on annotated data and improve the performance of multi-granularity academic function recognition tasks with a small number of labeled examples.
Optimizing Warfarin Dosing Using Contextual Bandit: An Offline Policy Learning and Evaluation Method
no code implementations • 16 Feb 2024 • Yong Huang, Charles A. Downs, Amir M. Rahmani
Warfarin, an anticoagulant medication, is formulated to prevent and address conditions associated with abnormal blood clotting, making it one of the most prescribed drugs globally.
ChunkAttention: Efficient Self-Attention with Prefix-Aware KV Cache and Two-Phase Partition
1 code implementation • 23 Feb 2024 • Lu Ye, Ze Tao, Yong Huang, Yang Li
In this paper, we introduce ChunkAttention, a prefix-aware self-attention module that can detect matching prompt prefixes across multiple requests and share their key/value tensors in memory at runtime to improve the memory utilization of KV cache.
Enhancing the "Immunity" of Mixture-of-Experts Networks for Adversarial Defense
no code implementations • 29 Feb 2024 • Qiao Han, Yong Huang, xinling Guo, Yiteng Zhai, Yu Qin, Yao Yang
Recent studies have revealed the vulnerability of Deep Neural Networks (DNNs) to adversarial examples, which can easily fool DNNs into making incorrect predictions.
MolNexTR: A Generalized Deep Learning Model for Molecular Image Recognition
1 code implementation • 6 Mar 2024 • Yufan Chen, Ching Ting Leung, Yong Huang, Jianwei Sun, Hao Chen, Hanyu Gao
In addition, it employs a series of novel augmentation algorithms to significantly enhance the robustness and performance of the model.