Search Results for author: Xuhong Zhang
Found 30 papers, 13 papers with code
TransLinkGuard: Safeguarding Transformer Models Against Model Stealing in Edge Deployment
no code implementations • 17 Apr 2024 • Qinfeng Li, Zhiqiang Shen, Zhenghan Qin, Yangfan Xie, Xuhong Zhang, Tianyu Du, Jianwei Yin
Specifically, we identify four critical protection properties that existing methods fail to simultaneously satisfy: (1) maintaining protection after a model is physically copied; (2) authorizing model access at request level; (3) safeguarding runtime reverse engineering; (4) achieving high security with negligible runtime overhead.
ERA-CoT: Improving Chain-of-Thought through Entity Relationship Analysis
1 code implementation • 11 Mar 2024 • Yanming Liu, Xinyue Peng, Tianyu Du, Jianwei Yin, Weihao Liu, Xuhong Zhang
Large language models (LLMs) have achieved commendable accomplishments in various natural language processing tasks.
RA-ISF: Learning to Answer and Understand from Retrieval Augmentation via Iterative Self-Feedback
1 code implementation • 11 Mar 2024 • Yanming Liu, Xinyue Peng, Xuhong Zhang, Weihao Liu, Jianwei Yin, Jiannan Cao, Tianyu Du
Large language models (LLMs) demonstrate exceptional performance in numerous tasks but still heavily rely on knowledge stored in their parameters.
PRSA: Prompt Reverse Stealing Attacks against Large Language Models
no code implementations • 29 Feb 2024 • Yong Yang, Xuhong Zhang, Yi Jiang, Xi Chen, Haoyu Wang, Shouling Ji, Zonghui Wang
In the mutation phase, we propose a prompt attention algorithm based on differential feedback to capture these critical features for effectively inferring the target prompts.
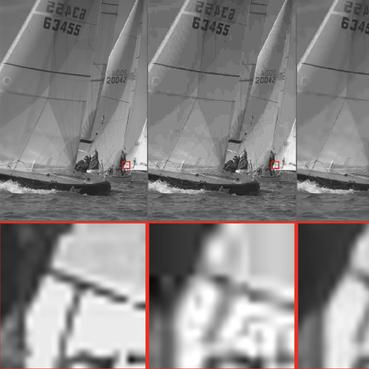
3D Volumetric Super-Resolution in Radiology Using 3D RRDB-GAN
no code implementations • 6 Feb 2024 • Juhyung Ha, Nian Wang, Surendra Maharjan, Xuhong Zhang
This study introduces the 3D Residual-in-Residual Dense Block GAN (3D RRDB-GAN) for 3D super-resolution for radiology imagery.
MEAOD: Model Extraction Attack against Object Detectors
no code implementations • 22 Dec 2023 • Zeyu Li, Chenghui Shi, Yuwen Pu, Xuhong Zhang, Yu Li, Jinbao Li, Shouling Ji
The widespread use of deep learning technology across various industries has made deep neural network models highly valuable and, as a result, attractive targets for potential attackers.
Let All be Whitened: Multi-teacher Distillation for Efficient Visual Retrieval
1 code implementation • 15 Dec 2023 • Zhe Ma, Jianfeng Dong, Shouling Ji, Zhenguang Liu, Xuhong Zhang, Zonghui Wang, Sifeng He, Feng Qian, Xiaobo Zhang, Lei Yang
Instead of crafting a new method pursuing further improvement on accuracy, in this paper we propose a multi-teacher distillation framework Whiten-MTD, which is able to transfer knowledge from off-the-shelf pre-trained retrieval models to a lightweight student model for efficient visual retrieval.
Improving the Robustness of Transformer-based Large Language Models with Dynamic Attention
no code implementations • 29 Nov 2023 • Lujia Shen, Yuwen Pu, Shouling Ji, Changjiang Li, Xuhong Zhang, Chunpeng Ge, Ting Wang
Extensive experiments demonstrate that dynamic attention significantly mitigates the impact of adversarial attacks, improving up to 33\% better performance than previous methods against widely-used adversarial attacks.
AdaCCD: Adaptive Semantic Contrasts Discovery Based Cross Lingual Adaptation for Code Clone Detection
no code implementations • 13 Nov 2023 • Yangkai Du, Tengfei Ma, Lingfei Wu, Xuhong Zhang, Shouling Ji
Code Clone Detection, which aims to retrieve functionally similar programs from large code bases, has been attracting increasing attention.
How ChatGPT is Solving Vulnerability Management Problem
no code implementations • 11 Nov 2023 • Peiyu Liu, Junming Liu, Lirong Fu, Kangjie Lu, Yifan Xia, Xuhong Zhang, Wenzhi Chen, Haiqin Weng, Shouling Ji, Wenhai Wang
Prior works show that ChatGPT has the capabilities of processing foundational code analysis tasks, such as abstract syntax tree generation, which indicates the potential of using ChatGPT to comprehend code syntax and static behaviors.
Facial Data Minimization: Shallow Model as Your Privacy Filter
no code implementations • 24 Oct 2023 • Yuwen Pu, Jiahao Chen, JiaYu Pan, Hao Li, Diqun Yan, Xuhong Zhang, Shouling Ji
Face recognition service has been used in many fields and brings much convenience to people.
CP-BCS: Binary Code Summarization Guided by Control Flow Graph and Pseudo Code
1 code implementation • 24 Oct 2023 • Tong Ye, Lingfei Wu, Tengfei Ma, Xuhong Zhang, Yangkai Du, Peiyu Liu, Shouling Ji, Wenhai Wang
Automatically generating function summaries for binaries is an extremely valuable but challenging task, since it involves translating the execution behavior and semantics of the low-level language (assembly code) into human-readable natural language.
Community-Based Hierarchical Positive-Unlabeled (PU) Model Fusion for Chronic Disease Prediction
1 code implementation • 6 Sep 2023 • Yang Wu, Xurui Li, Xuhong Zhang, Yangyang Kang, Changlong Sun, Xiaozhong Liu
Positive-Unlabeled (PU) Learning is a challenge presented by binary classification problems where there is an abundance of unlabeled data along with a small number of positive data instances, which can be used to address chronic disease screening problem.
Efficient Query-Based Attack against ML-Based Android Malware Detection under Zero Knowledge Setting
1 code implementation • 5 Sep 2023 • Ping He, Yifan Xia, Xuhong Zhang, Shouling Ji
The widespread adoption of the Android operating system has made malicious Android applications an appealing target for attackers.
Tram: A Token-level Retrieval-augmented Mechanism for Source Code Summarization
1 code implementation • 18 May 2023 • Tong Ye, Lingfei Wu, Tengfei Ma, Xuhong Zhang, Yangkai Du, Peiyu Liu, Shouling Ji, Wenhai Wang
In this paper, we propose a fine-grained Token-level retrieval-augmented mechanism (Tram) on the decoder side rather than the encoder side to enhance the performance of neural models and produce more low-frequency tokens in generating summaries.
Diff-ID: An Explainable Identity Difference Quantification Framework for DeepFake Detection
no code implementations • 30 Mar 2023 • Chuer Yu, Xuhong Zhang, Yuxuan Duan, Senbo Yan, Zonghui Wang, Yang Xiang, Shouling Ji, Wenzhi Chen
We then visualize the identity loss between the test and the reference image from the image differences of the aligned pairs, and design a custom metric to quantify the identity loss.
Watch Out for the Confusing Faces: Detecting Face Swapping with the Probability Distribution of Face Identification Models
no code implementations • 23 Mar 2023 • Yuxuan Duan, Xuhong Zhang, Chuer Yu, Zonghui Wang, Shouling Ji, Wenzhi Chen
We reflect this nature with the confusion of a face identification model and measure the confusion with the maximum value of the output probability distribution.
Edge Deep Learning Model Protection via Neuron Authorization
1 code implementation • 22 Mar 2023 • Jinyin Chen, Haibin Zheng, Tao Liu, Rongchang Li, Yao Cheng, Xuhong Zhang, Shouling Ji
With the development of deep learning processors and accelerators, deep learning models have been widely deployed on edge devices as part of the Internet of Things.
FreeEagle: Detecting Complex Neural Trojans in Data-Free Cases
1 code implementation • 28 Feb 2023 • Chong Fu, Xuhong Zhang, Shouling Ji, Ting Wang, Peng Lin, Yanghe Feng, Jianwei Yin
Thus, in this paper, we propose FreeEagle, the first data-free backdoor detection method that can effectively detect complex backdoor attacks on deep neural networks, without relying on the access to any clean samples or samples with the trigger.
TextDefense: Adversarial Text Detection based on Word Importance Entropy
no code implementations • 12 Feb 2023 • Lujia Shen, Xuhong Zhang, Shouling Ji, Yuwen Pu, Chunpeng Ge, Xing Yang, Yanghe Feng
TextDefense differs from previous approaches, where it utilizes the target model for detection and thus is attack type agnostic.
HashVFL: Defending Against Data Reconstruction Attacks in Vertical Federated Learning
no code implementations • 1 Dec 2022 • Pengyu Qiu, Xuhong Zhang, Shouling Ji, Chong Fu, Xing Yang, Ting Wang
Our work shows that hashing is a promising solution to counter data reconstruction attacks.
Hijack Vertical Federated Learning Models As One Party
no code implementations • 1 Dec 2022 • Pengyu Qiu, Xuhong Zhang, Shouling Ji, Changjiang Li, Yuwen Pu, Xing Yang, Ting Wang
Vertical federated learning (VFL) is an emerging paradigm that enables collaborators to build machine learning models together in a distributed fashion.
Label Inference Attacks Against Vertical Federated Learning
2 code implementations • USENIX Security 22 2022 • Chong Fu, Xuhong Zhang, Shouling Ji, Jinyin Chen, Jingzheng Wu, Shanqing Guo, Jun Zhou, Alex X. Liu, Ting Wang
However, we discover that the bottom model structure and the gradient update mechanism of VFL can be exploited by a malicious participant to gain the power to infer the privately owned labels.
"Is your explanation stable?": A Robustness Evaluation Framework for Feature Attribution
no code implementations • 5 Sep 2022 • Yuyou Gan, Yuhao Mao, Xuhong Zhang, Shouling Ji, Yuwen Pu, Meng Han, Jianwei Yin, Ting Wang
Experiment results show that the MeTFA-smoothed explanation can significantly increase the robust faithfulness.
Improving Long Tailed Document-Level Relation Extraction via Easy Relation Augmentation and Contrastive Learning
no code implementations • 21 May 2022 • Yangkai Du, Tengfei Ma, Lingfei Wu, Yiming Wu, Xuhong Zhang, Bo Long, Shouling Ji
Towards real-world information extraction scenario, research of relation extraction is advancing to document-level relation extraction(DocRE).
 Ranked #25 on
Relation Extraction
on DocRED
Ranked #25 on
Relation Extraction
on DocRED
Transfer Attacks Revisited: A Large-Scale Empirical Study in Real Computer Vision Settings
no code implementations • 7 Apr 2022 • Yuhao Mao, Chong Fu, Saizhuo Wang, Shouling Ji, Xuhong Zhang, Zhenguang Liu, Jun Zhou, Alex X. Liu, Raheem Beyah, Ting Wang
To bridge this critical gap, we conduct the first large-scale systematic empirical study of transfer attacks against major cloud-based MLaaS platforms, taking the components of a real transfer attack into account.
Seeing is Living? Rethinking the Security of Facial Liveness Verification in the Deepfake Era
no code implementations • 22 Feb 2022 • Changjiang Li, Li Wang, Shouling Ji, Xuhong Zhang, Zhaohan Xi, Shanqing Guo, Ting Wang
Facial Liveness Verification (FLV) is widely used for identity authentication in many security-sensitive domains and offered as Platform-as-a-Service (PaaS) by leading cloud vendors.
NeuronFair: Interpretable White-Box Fairness Testing through Biased Neuron Identification
1 code implementation • 25 Dec 2021 • Haibin Zheng, Zhiqing Chen, Tianyu Du, Xuhong Zhang, Yao Cheng, Shouling Ji, Jingyi Wang, Yue Yu, Jinyin Chen
To overcome the challenges, we propose NeuronFair, a new DNN fairness testing framework that differs from previous work in several key aspects: (1) interpretable - it quantitatively interprets DNNs' fairness violations for the biased decision; (2) effective - it uses the interpretation results to guide the generation of more diverse instances in less time; (3) generic - it can handle both structured and unstructured data.
Backdoor Pre-trained Models Can Transfer to All
1 code implementation • 30 Oct 2021 • Lujia Shen, Shouling Ji, Xuhong Zhang, Jinfeng Li, Jing Chen, Jie Shi, Chengfang Fang, Jianwei Yin, Ting Wang
However, a pre-trained model with backdoor can be a severe threat to the applications.
Constructing Contrastive samples via Summarization for Text Classification with limited annotations
1 code implementation • Findings (EMNLP) 2021 • Yangkai Du, Tengfei Ma, Lingfei Wu, Fangli Xu, Xuhong Zhang, Bo Long, Shouling Ji
Unlike vision tasks, the data augmentation method for contrastive learning has not been investigated sufficiently in language tasks.